CCNP Routing and Switching SWITCH 300-115 Official Cert Guide (2015)
Part V. Monitoring Campus Networks
Chapter 14. Managing Switches with SNMP
This chapter covers the following topics that you need to master for the CCNP SWITCH exam:
![]() SNMP Overview: This section discusses SNMP basics such as the system roles, data organization, data operations, and SNMP versions.
SNMP Overview: This section discusses SNMP basics such as the system roles, data organization, data operations, and SNMP versions.
![]() Configuring SNMP: This section explains the steps and commands required to configure each SNMP version on a switch.
Configuring SNMP: This section explains the steps and commands required to configure each SNMP version on a switch.
The Simple Network Management Protocol (SNMP) can be used to manage switches and other network devices remotely, usually from a central network management platform. This chapter discusses three versions of SNMP that you can leverage to lighten the administrative load when you are monitoring or configuring many switches.
“Do I Know This Already?” Quiz
The “Do I Know This Already?” quiz allows you to assess whether you should read this entire chapter thoroughly or jump to the “Exam Preparation Tasks” section. If you are in doubt based on your answers to these questions or your own assessment of your knowledge of the topics, read the entire chapter. Table 14-1 outlines the major headings in this chapter and the “Do I Know This Already?” quiz questions that go with them. You can find the answers in Appendix A, “Answers to the ‘Do I Know This Already?’ Quizzes.”

Table 14-1 “Do I Know This Already?” Foundation Topics Section-to-Question Mapping
1. SNMP access is configured on a switch. Which one of the following roles does the switch play during SNMP communication?
a. SNMP agent
b. SNMP server
c. SNMP manager
d. SNMP responder
2. Which one of the following contains information about a switch, its interfaces, and many other counters and statistics?
a. FIB
b. RIB
c. MIB
d. OID
3. SNMP communication utilizes which one of the following protocols and port numbers?
a. GRE port 2
b. UDP port 112
c. TCP port 21
d. UDP port 161
e. TCP port 443
4. Which one of the following event message types is sent via SNMP and must be acknowledged?
a. SNMP poll
b. SNMP trap
c. SNMP inform
d. SNMP alarm
5. Which one of the following credentials does SNMPv1 use to authenticate management platforms?
a. Username
b. Community string
c. Group name
d. Certificate
6. Which SNMP version can use MD5 or SHA as a security means to authenticate packets?
a. SNMPv1
b. SNMPv2
c. SNMPv2C
d. SNMPv3
7. The snmp-server host command is used to define which one of the following?
a. The polling SNMP manager
b. The SNMP user’s machine
c. The machine that will receive traps and informs
d. The machines that are allowed to poll
8. SNMPv3 can leverage which of the following attributes to control access to switch information? (Choose all that apply.)
a. SNMP group
b. SNMP user
c. IP address
d. SNMP view
e. All of these answers are correct.
Foundation Topics
SNMP Overview
The Simple Network Management Protocol (SNMP) enables a network device to share information about itself and its activities. A complete SNMP system consists of the following parts:

![]() SNMP manager: A network management system that uses SNMP to poll and receive data from any number of network devices. The SNMP manager usually is an application that runs in a central location.
SNMP manager: A network management system that uses SNMP to poll and receive data from any number of network devices. The SNMP manager usually is an application that runs in a central location.
![]() SNMP agent: A process that runs on the network device being monitored. All types of data are gathered by the device itself and stored in a local database. The agent can then respond to SNMP polls and queries with information from the database, and it can send unsolicited alerts or “traps” to an SNMP manager.
SNMP agent: A process that runs on the network device being monitored. All types of data are gathered by the device itself and stored in a local database. The agent can then respond to SNMP polls and queries with information from the database, and it can send unsolicited alerts or “traps” to an SNMP manager.
In the case of Catalyst switches in the network, each switch automatically collects data about itself, its resources, and each of its interfaces. This data is stored in a Management Information Base (MIB) database in memory and is updated in real time.
The MIB is organized in a structured, hierarchical fashion, forming a tree structure. In fact, the entire MIB is really a collection of variables that are stored in individual, more granular MIBs that form the branches of the tree. Each MIB is based on the Abstract Syntax Notation 1 (ASN.1) language. Each variable in the MIB is referenced by an object identifier (OID), which is a long string of concatenated indexes that follow the path from the root of the tree all the way to the variable’s location. For example, a counter for the number of inbound bytes on an interface can be found at OID 1.3.6.1.2.1.2.2.1.10 in the IF (interface) MIB.
Fortunately, only the SNMP manager and agent need to be concerned with interpreting the MIBs. As far as the SWITCH exam and course go, you should just be aware that the MIB structure exists and that it contains everything about a switch that can be monitored.
To see any of the MIB data, an SNMP manager must send an SNMP poll or query to the switch. The query contains the OID of the specific variable being requested so that the agent running on the switch knows what information to return. An SNMP manager can use the following mechanisms to communicate with an SNMP agent, all over UDP port 161:
![]() Get request: The value of one specific MIB variable is needed.
Get request: The value of one specific MIB variable is needed.
![]() Get next request: The next or subsequent value following an initial get request is needed.
Get next request: The next or subsequent value following an initial get request is needed.
![]() Get bulk request: Whole tables or lists of values in a MIB variable are needed.
Get bulk request: Whole tables or lists of values in a MIB variable are needed.
![]() Set request: A specific MIB variable needs to be set to a value.
Set request: A specific MIB variable needs to be set to a value.
SNMP polls or requests are usually sent by the SNMP manager at periodic intervals. This makes real-time monitoring difficult because changing variables will not be noticed until the next poll cycle. However, SNMP agents can send unsolicited alerts to notify the SNMP manager of real-time events at any time. Alerts can be sent using the following mechanisms over UDP port 162:
![]() SNMP trap: News of an event (interface state change, device failure, and so on) is sent without any acknowledgment that the trap has been received.
SNMP trap: News of an event (interface state change, device failure, and so on) is sent without any acknowledgment that the trap has been received.
![]() Inform request: News of an event is sent to an SNMP manager, and the manager is required to acknowledge receipt by echoing the request back to the agent.
Inform request: News of an event is sent to an SNMP manager, and the manager is required to acknowledge receipt by echoing the request back to the agent.
As network management has evolved, SNMP has developed into three distinct versions. The original, SNMP Version 1 (SNMPv1), is defined in RFC 1157. It uses simple one-variable Get and Set requests, along with simple SNMP traps. SNMP managers can gain access to SNMP agents by matching a simple “community” text string. When a manager wants to read or write a MIB variable on a device, it sends the community string in the clear, as part of the request. The request is granted if that community string matches the agent’s community string.
In theory, only managers and agents belonging to the same community should be able to communicate. In practice, any device has the potential to read or write variables to an agent’s MIB database by sending the right community string, whether it is a legitimate SNMP manager or not. This creates a huge security hole in SNMPv1.
The second version of SNMP, SNMPv2C (RFC 1901), was developed to address some efficiency and security concerns. For example, SNMPv2C adds 64-bit variable counters, extending the useful range of values over the 32-bit counters used in SNMPv1. With 64-bit counters, a switch can keep track of very large numbers, such as byte counters found on high-speed interfaces.
In addition, SNMPv2C offers the bulk request, by which MIB variables can be retrieved in a bulk form with a single request. Event notifications sent from an SNMPv2C agent can be in the form of SNMP traps or inform requests. The latter form requires an acknowledgment from the SNMP manager that the inform message was received. Despite the intentions of its developers, SNMPv2C does not address any security concerns over that of SNMPv1. In addition, there were other implementations of SNMPv2 that were incompatible with SNMPv2C, which acted as a further deterrent to its acceptance.
The third generation of SNMP, SNMPv3, is defined in RFCs 3410 through 3415. It addresses the security features that are lacking in the earlier versions. SNMPv3 can authenticate SNMP managers through usernames. When usernames are configured on the SNMP agent of a switch, they can be organized into SNMPv3 group names. In addition, access to MIB information can be controlled on a per-group basis. You can configure a “view” that defines which MIB variable trees can be read or written.
Each SNMPv3 group is defined with a security level that describes the extent to which the SNMP data will be protected. Data packets can be authenticated to preserve their integrity, encrypted to obscure their contents, or both. The following security levels are available. The naming scheme uses auth to represent packet authentication and priv to represent data privacy or encryption:
![]() noAuthNoPriv: SNMP packets are neither authenticated nor encrypted.
noAuthNoPriv: SNMP packets are neither authenticated nor encrypted.
![]() authNoPriv: SNMP packets are authenticated but not encrypted.
authNoPriv: SNMP packets are authenticated but not encrypted.
![]() authPriv: SNMP packets are authenticated and encrypted.
authPriv: SNMP packets are authenticated and encrypted.
As a best practice, you should use SNMPv3 to leverage its superior security features whenever possible. If you must use SNMPv1 for a device, you should configure the switch to limit SNMP access to a read-only role. Never permit read-write access because the simple community string authentication can be exploited to make unexpected changes to a switch configuration.
Catalyst switches offer one additional means of limiting SNMP access—an access list can be configured to permit only specific (and known) SNMP manager IP addresses. You should configure and apply an access list to your SNMP configurations whenever possible.
Because SNMP is a universal method for monitoring all sorts of network devices, it is not unique to LAN switches. Therefore, you should understand the basics of how SNMP works, the differences between the different SNMP versions, and how you might apply SNMP to monitor a switched network. You can use Table 14-2 as a memory aid for your exam study.

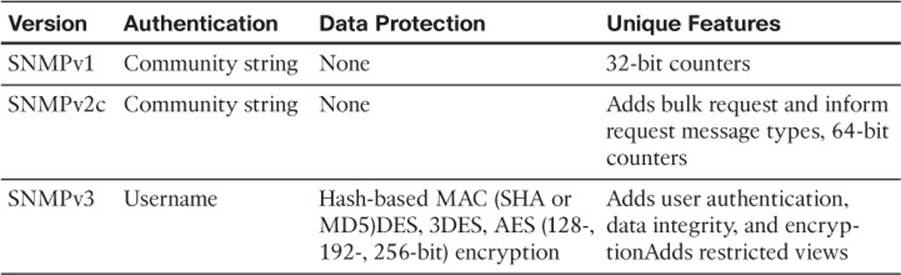
Table 14-2 Comparison of SNMP Versions and Features
Configuring SNMP
SNMP is normally available in three versions. As a best practice, though, you should use SNMPv3. You can find information about configuring all three versions in the sections that follow.
Configuring SNMPv1
You should be familiar with the basic SNMPv1 configuration. Fortunately, this involves just a few commands, as follows:
Switch(config)# access-list access-list-number permit ip-addr
Switch(config)# snmp-server community community-string [ro | rw] [access-list-
number]
!
Switch(config)# snmp-server host host-address community-string [trap-type]
First, define a standard IP access list that permits only the IP addresses of your SNMP agent machines. Then apply that access list to the SNMPv1 community string with the snmp-server community command. Use the ro keyword to allow read-only access by the SNMP manager; otherwise, you can use the rw keyword to allow both read and write access.
Finally, use the snmp-server host command to identify the IP address of the SNMP manager where SNMP traps will be sent. By default, all types of traps are sent. You can use the ? key in place of trap-type to see a list of the available trap types.
In Example 14-1, the switch is configured to allow SNMP polling from network management stations at 192.168.3.99 and 192.168.100.4 only. The community string MonitorIt is used to authenticate the SNMP requests. All possible SNMP traps are sent to 192.168.3.99.
Example 14-1 Configuring SNMPv1 Access
Switch(config)# access-list 10 permit 192.168.3.99
Switch(config)# access-list 10 permit 192.168.100.4
Switch(config)# snmp-server community MonitorIt ro 10
Switch(config)# snmp-server host 192.168.3.99 MonitorIt
Configuring SNMPv2C
Configuring SNMPv2C is similar to configuring SNMPv1. The only difference is with SNMP trap or inform configuration. You can use the following commands to configure basic SNMPv2C operation:
Switch(config)# access-list access-list-number permit ip-addr
Switch(config)# snmp-server community string [ro | rw] [access-list-number]
!
Switch(config)# snmp-server host host-address [informs] version 2c community-
string
In the snmp-server host command, use the version 2c keywords to identify SNMPv2C operation. By default, regular SNMP traps are sent. To use inform requests instead, add the informs keyword.
Configuring SNMPv3

SNMPv3 configuration is a bit more involved than versions 1 or 2C, due mainly to the additional security features. You can use the following steps to configure SNMPv3 on a switch:
Step 1. You can limit which hosts can access the switch via SNMP by defining a named or numbered IP access list. Permitted addresses will be given SNMPv3 access.
Step 2. You can use the snmp-server view command to define a specific view for the users. Only the MIB variables located under the OID name given as oid-tree will be visible to the user group. For example, ifAdminStatus contains the interface administrative status, ifDescr contains the interface description, and so on. You can repeat the snmp-server view command to add additional OID names to the view:
Switch(config)# snmp-server view view-name oid-tree
If no view is configured, all MIB variables are visible to the users.
Step 3. Use the snmp-server group command to configure a group name that will set the security level policies for SNMPv3 users that are assigned to the group. The security level is defined by the noauth (no packet authentication or encryption), auth (packets are authenticated but not encrypted), or priv (packets are both authenticated and encrypted) keyword. Only the security policy is defined in the group; no passwords or keys are required yet.
Tip
The SNMPv3 priv keyword and packet encryption can be used only if the switch is running a cryptographic version of its Cisco IOS Software image. The auth keyword and packet authentication can be used regardless.
If you configured a view, you can use the read, write, and notify keywords to limit access to read, write, or notification operations. If you configured an access list, you can apply it to the group with the access keyword:
Switch(config)# snmp-server group group-name v3 {noauth | auth | priv}
[read read-view] [write write-view] [notify notify-view] [access access-
list]
Step 4. Define a username that an SNMP manager will use to communicate with the switch. Use the snmp-server user command to define the user-name and associate it with the SNMPv3 group-name. The v3 keyword configures the user to use SNMPv3.
The SNMPv3 user must also have some specifics added to its security policy. Use the auth keyword to define either message digest 5 (MD5) authentication or the secure hash algorithm (SHA) as the packet authentication method, along with the auth-password text string that will be used in the hash computation. The priv keyword defines the encryption method (DES, 3DES, or AES 128/192/256-bit) and the priv-password text string that will be used in the encryption algorithm.
Switch(config)# snmp-server user user-name group-name v3 auth {md5 |
sha} auth-password priv {des | 3des | aes {128 | 192 | 256} priv-
password [access-list-number]
The same SNMPv3 username, authentication method and password, and encryption method and password must also be defined on the SNMP manager so it can successfully talk to the switch.
Step 5. You can use the snmp-server host command to identify the SNMP manager that will receive either traps or informs. The switch can use SNMPv3 to send traps and informs, using the security parameters that are defined for the SNMPv3 username:
Switch(config)# snmp-server host host-address [informs] version 3
{noauth | auth |priv} username [trap-type]
In Example 14-2, a switch is configured for SNMPv3 operation. Access list 10 permits only stations at 192.168.3.99 and 192.168.100.4 with SNMP access. SNMPv3 access is defined for a group named NetOps using the priv (authentication and encryption) security level. One SNMPv3, a user named mymonitor, is defined; the network management station will use that username when it polls the switch for information. The username will require SHA packet authentication and AES-128 encryption, using the s3cr3tauth and s3cr3tpr1v passwords, respectively.
Finally, SNMPv3 informs will be used to send alerts to station 192.168.3.99 using the priv security level and username mymonitor.
Example 14-2 Configuring SNMPv3 Access
Switch(config)# access-list 10 permit 192.168.3.99
Switch(config)# access-list 10 permit 192.168.100.4
Switch(config)# snmp-server group NetOps v3 priv
Switch(config)# snmp-server user mymonitor NetOps v3 auth sha s3cr3tauth priv aes
128 s3cr3tpr1v 10
Switch(config)# snmp-server host 192.168.3.99 informs version 3 priv mymonitor
Exam Preparation Tasks
Review All Key Topics
Review the most important topics in the chapter, noted with the Key Topic icon in the outer margin of the page. Table 14-3 lists a reference of these key topics and the page numbers on which each is found.

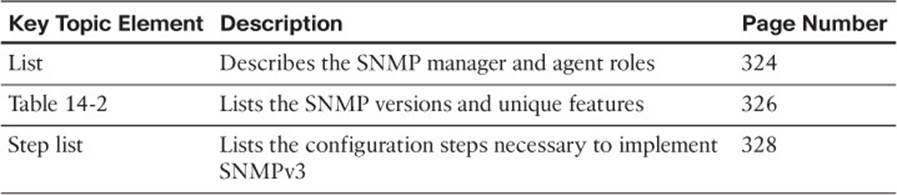
Table 14-3 Key Topics for Chapter 14
Complete Tables and Lists from Memory
Print a copy of Appendix C, “Memory Tables,” (found on the CD), or at least the section for this chapter, and complete the tables and lists from memory. Appendix D, “Memory Table Answer Key,” also on the CD, includes completed tables and lists to check your work.
Define Key Terms
Define the following key terms from this chapter, and check your answers in the glossary:
MIB
OID
Simple Network Management Protocol (SNMP)
SNMP manager
SNMP agent
SNMP inform
SNMP trap
Use Command Reference to Check Your Memory
This section includes the most important configuration and EXEC commands covered in this chapter. It might not be necessary to memorize the complete syntax of every command, but you should remember the basic keywords that are needed.
To test your memory of the SNMP configuration commands, cover the right side of Table 14-4 with a piece of paper, read the description on the left side, and then see how much of the command you can remember.
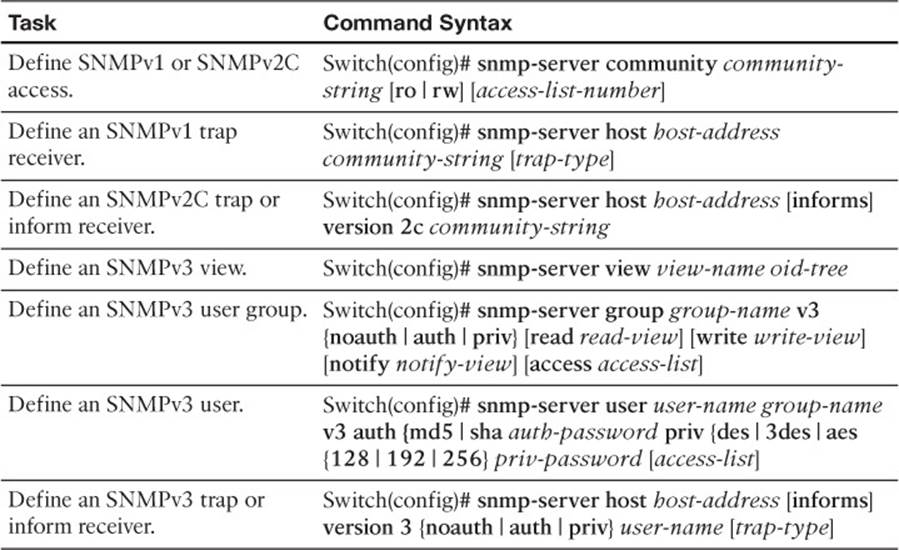
Table 14-4 SNMP Configuration Commands