Praise for Hacking Exposed: Unified communications & VoIP Security Secrets & Solutions, Second Edition (2014)
PART IV. UC SESSION AND APPLICATION HACKING
CHAPTER 17. EMERGING TECHNOLOGIES
The best way to get hold of me is over Cisco Jabber. I am always in meetings and can’t usually take calls.
If it is really important, send me a text message.
I will Skype you later.
Someone left me a voicemail—how in the world do I get to it?
—Typical quotes from enterprise UC users
Unified Communications (UC) has the promise to increase enterprise productivity and lower infrastructure costs. The definition of UC depends on who is defining it. However, as we have said before, we think of UC as the combination of multiple real-time communications technologies, including voice, VoIP, video, messaging, presence, and social networking. Although voice remains the predominant form of communications for enterprises, its role is definitely changing. Historically, voice was the primary (if not only) way that people communicated remotely. Aside from physical interaction, letters, and more recently email, voice was pretty much what you used. Also, voice wasn’t always available, because you had to have access to a telephone. “Long-distance” and international calls were expensive, so you also had to be aware of where and when you called. Enterprise voice systems were delivered from a small set of vendors, and the majority of local and long distance access was provided by a small set of service providers.
Now things are very different, and they are changing more rapidly than ever before. We have seen more changes in enterprise and consumer communications in the past five years than we have seen in the previous 100 years. Enterprise voice has largely migrated to VoIP. Enterprise voice services are available from more vendors, including powerful new UC-focused players such as Microsoft with their Lync offering. Voice is cheaper and even free if you are willing to use cloud-based over-the-top (OTT) services such as Skype, Viber, Line, Google Voice, and other offerings. Many voice conversations occur over these applications and mobile smartphones, even when an enterprise phone is available. Mobility and smartphones, with cheap unlimited calling plans, have increased the use of cellular voice, allow users to be in touch constantly, and also provide a platform that is always connected to the Internet, thus enabling new forms of communication.
You also have many alternatives to voice for communication. Although nothing beats having a voice conversation, other modes of communications such as video, text messaging, “instant” messaging, and social networking dominate our “conversations”—especially among consumers and younger people. Some of these forms of communications are making their way into the enterprise. Often a quick text message is preferable to a voice call. Many of us, especially younger individuals, will send over 100 text messages a day. Users are constantly communicating via messages, pictures, and videos on social networking sites such as Twitter, Facebook, Vine, Instagram, and so on. These users are constantly connected and communicating through their Apple, Android, and other smartphones. Enterprises have recognized the users’ dependence on these devices and have largely adopted a bring-your-own-device (BYOD) policy, which means that those enterprises allows business use on the device selected by the consumer.
Most of these communication services are delivered via the public cloud rather than through traditional enterprise systems. These services are using the Internet more and more rather than the traditional public voice network and fixed trunking. The cloud is even being used to host traditional voice systems. The old concept of Centrex is much more attractive and cost-effective using UC, where the IP PBX and other systems are resident in the cloud and the Internet is used to deliver service. Finally, entire new protocols are available, such as WebRTC, where everything you need to make voice and video calls is built into the web browser, offering to move even more communications to the Internet and the “cloud.”
Many of these technologies have been in place for a while and aren’t necessarily “emerging,” but they need to be mentioned because their use is increasing within the enterprise. The next few sections cover these technologies, address how they are used within enterprises, and summarize which security issues are present.
Other Enterprise UC Systems
Enterprise UC systems have many providers. A few vendors dominate this industry, with many others occupying market niches such as contact centers and small enterprises. The largest vendors are Cisco, Avaya (who purchased Nortel in 2009), NEC, and Siemens. Figure 17-1 shows a 2013 Infonetics report that compares the relative market share of the major UC vendors.
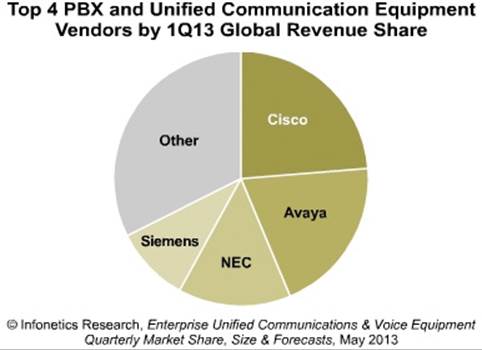
Figure 17-1 Market share of major IP PBX/VoIP/UC vendors
It is difficult to predict the future, but we expect that Cisco will continue to gain market share, whereas vendors such as Avaya, NEC, and Siemens are likely to lose overall share or succeed only in certain niches. Although it is not yet shown in this chart, we predict that Microsoft Lync will increase its market share and become a dominant player in enterprise UC.
The first version of this book included chapters on Cisco, Avaya, and Asterisk. For this version, we chose to focus more on attacks that affect all enterprise systems, regardless of the UC vendor chosen. Recall from Part II of the book that if an attacker wants to flood an enterprise with TDoS, call pumping, voice SPAM, voice phishing, and some types of fraud calls, they do not need to know what type of UC system is present. In Part III of this book, most of the VoIP-specific attacks covered include eavesdropping, infrastructure attacks, different types of packet floods, and can again affect any UC system. Part IV of the book includes the SIP and RTP attacks, which can affect any UC system or component using these protocols. The point of this is that there are plenty of effective attacks without focusing on the specifics of each vendor’s implementation.
We did provide a chapter for Cisco, not because their security is poor—quite the opposite; they are industry leaders—but because they are the market leader and own the underlying switching infrastructure. Therefore, even if an enterprise uses another UC vendor, there is an 80–85 percent chance they are using Cisco for networking. We elected to remove the chapters on Avaya and Asterisk because, in our opinion, Avaya’s market share is declining and Asterisk is not commonly used by enterprises (although it is a great attack platform, which we covered extensively throughout the book).
One UC vendor we will cover briefly is Microsoft and their product Lync, which is a full and compelling UC offering. In the past, Microsoft’s offering was more of a UC veneer over the existing IP PBX, but not a full replacement. We predict that over the coming years Microsoft Lync will continue to gain market share and become a dominant player in this industry.
Microsoft Lync
Microsoft Lync is a complete UC solution based on and integrated with familiar productivity tools, including Microsoft Office, Outlook, softphones, instant messaging, presence, and Skype, all neatly combined for the user. Microsoft also offers all the underlying software infrastructure elements (operating systems, databases, and so on), coupled with a robust software interface to hardware elements (servers, routers, SBCs, and so on), all integrated to support a variety of enterprise implementations. Lync not only ties together existing infrastructure elements, it also allows for the consolidation and replacement of existing elements.
Microsoft Lync itself only consists of software components. It maintains a model of certifying software and hardware devices as being Lync compliant. This certification allows end users to be sure that third-party software and hardware will fit into their Lync implementation. The key to Lync certification is achieved through the standardization of Lync interfaces. Lync interfaces are supported by a robust set of application programming interfaces (APIs) published by Microsoft and implemented by third-party suppliers. The Lync platform supports several important features for the enterprise, including the following:
•Compatibility Backward and forward compatibility for existing and future communication and productivity paradigms
• Security A secure platform for diverse and complex enterprises
• Maintainability/scalability A maintainable and scalable platform to accommodate growth and expansion within the enterprise, without the need to “fork-lift” out old technologies
Lync is designed to be deployed into existing enterprise infrastructures with minimal disruption to users. Lync also provides a path forward for new enterprise technologies (video, Skype, and so on), as well as new infrastructure topologies (cloud-based services, remote users, and so on). To achieve this, Microsoft has designed Lync to utilize an enterprise’s existing data and telecommunications deployments (typically composed of onsite equipment that supports onsite employees), but that easily allows for migration to new infrastructure topologies (such as cloud-based services and employees working at remote locations). This deployment strategy not only allows Lync to provide backward compatibility to existing systems, but also provides a path forward to new infrastructure topologies and productivity tools. All of these topologies and tools are meant to meet future ways that users will be federated to the enterprise.
Another particular strength of Lync is its support for small, medium, and large enterprises. It can be successfully deployed in a significant number of topologies as well. Microsoft provides reference designs for small, medium, and large enterprises.1 We include the reference diagram for a medium enterprise in Figure 17-2.
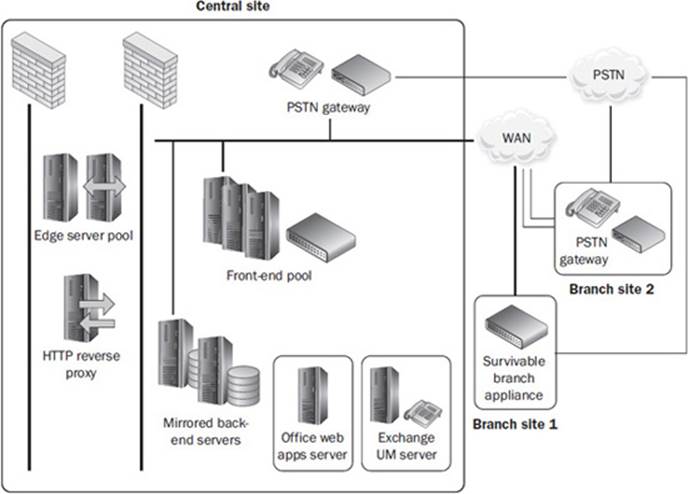
Figure 17-2 Lync medium enterprise architecture
Currently, Lync can be deployed in several configurations, including the following:
• Completely internal to the enterprise All hardware and software is hosted and controlled internal to the company.
• Completely external to the enterprise All hardware and software is hosted externally in the cloud, or as a service from an external UC provider.
• Hybrid combination of internal and external Some elements may utilize existing or legacy systems, whereas other functionality is provided by external UC provider.
By supporting these UC configurations, Lync is very scalable, allowing enterprises to support their existing UC infrastructure, add new or expanded access to UC features, or transition to more economical UC solutions. This scalability also provides flexibility. As the enterprise transitions to new ways of doing business, or as employees adapt to new modalities of interfacing with the enterprise, Lync can support diverse and changing installations.
As the enterprise expands or contracts, Lync architecture can also support diverse back-end topologies. Lync can be configured to dynamically support high availability, load balancing, resource/trunk pools, and database performance/persistence. Each of these components is extremely configurable, and can be added or removed from the enterprise’s Lync installation.
Lync also bridges the gap between the data world (that is, the cloud) and the communications world (PSTN, VoIP, and mobile). As the data and communications worlds continue to merge, the distinction between “types” of information (IP versus analog or data versus voice, for example) will ultimately disappear. The integration of Skype into Lync will further facilitate the transition from traditional telephony infrastructure to a pure IP voice/video infrastructure.
Lync maintainability is enabled by a central management store (CMS). The topology and user configuration are stored in a Microsoft SQL database. Lync supports all the aspects of a modern database implementation (scalability, replication, backup, and so on). Figure 17-3 shows the main administrative user interface for Lync, along with policy control functions.
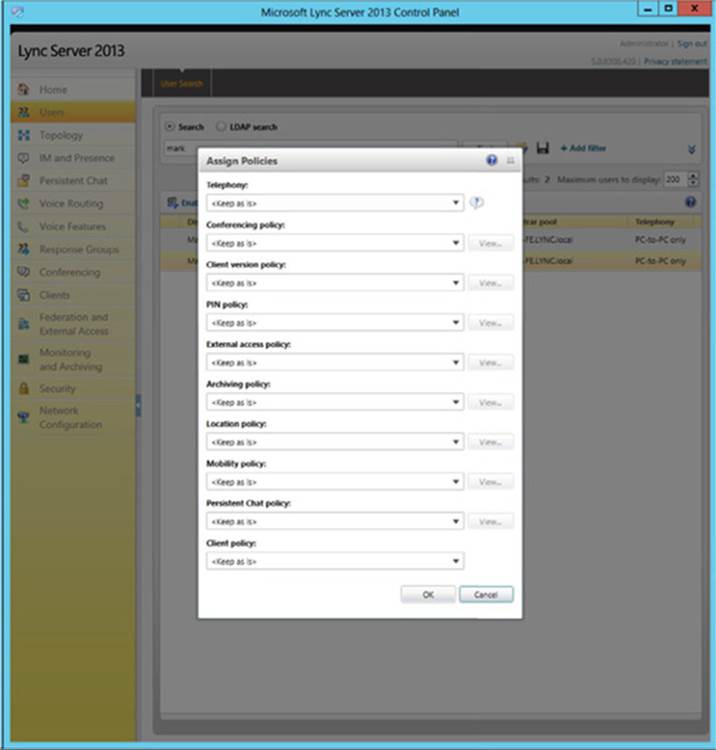
Figure 17-3 Lync administrative interface
Security
Security has been deeply engrained into Lync. By design, the Lync infrastructure requires secure user, application, and machine interfaces. This mandated protection includes the following:
• Authentication Enforced through Windows/domain authentication
• User permissions Enforced through Active Directory
• Machine and service hiding Enforced through strict DNS resolution
• Web services Enforced through certificate authorization
• Machine-to-machine communication Enforced through mandatory protocols such as secure SIP/TLS and SRTP
A unique aspect of Lync is that all communications for SIP and RTP are encrypted and authenticated by default. This makes most of the SIP and RTP attacks discussed in Part IV of the book ineffective. Microsoft reports Lync security issues on their main security page.2 An example of a recent “important” Lync vulnerability is provided as well.3
Note![]()
Microsoft Lync provides a very rich set of APIs known as the Unified Communications Managed API (UCMA). One possible application of this API is to build an outgoing dialer, which could be used for robocalls for voice SPAM, voice phishing, TDoS, and so on.4
Over-the-Top (OTT)/Internet Softphone Applications
Over-the-top (OTT) in this context refers to a voice softphone application that uses the Internet rather than the traditional public voice network. Although voice service, long distance, and international calling have gotten cheaper, some calls to certain destinations aren’t free. This is especially an issue for consumers, students, and individuals who need to make many international calls. These softphone applications offer a free alternative to landline, cellular, and enterprise voice services. Consumers and enterprises use OTT applications such as Skype to make free voice calls, along with using other forms of communications such as video chat and messaging.
Many softphone applications are available now, including Skype, Viber, Line, and Whatsapp. Skype remains the most common and widely used service, but new softphone applications are coming along all the time. All of these softphones require you to install them on your PC, Mac, tablet, or smartphone. These applications do not federate with one another, so you can only communicate with users who are using the same application. Some applications, including Skype, for example, do allow for hopping off to the public voice network.
The softphone applications run on your smartphone, tablet, or laptop and maintain a connection over the Internet. In an enterprise setting, this creates a number of security issues. For one, many applications require that specific ports be opened up on the host and/or corporate firewall so the applications operate correctly, typically including a large range of high-numbered open ports for audio. An attacker may be able to compromise your platform through the softphone application by gaining access to the underlying operating system. Likewise, if an attacker has access to the underlying operating system, they may be able to monitor conversations. Any application can also be used for unmonitored communications, which may include proprietary data (this is more of an issue for the messaging capability that is often bundled with the softphone application).
A number of companies offer alternatives to traditional residential phone services, including Vonage, MagicJack, and cable offerings. These primarily consumer offerings allow using a traditional analog phone, but then use VoIP and, in some cases, the Internet for service, with hop off to the public voice network. These services offer consumers phone service for a low flat rate. They have the advantage that you can use your normal old phone rather than some application on a computer, laptop, or smartphone, which is attractive to some users.
Again, most of these OTT applications are consumer oriented. One exception is Skype, which although hardly an emerging technology is gaining use within the enterprise. With its integration with Microsoft Lync (and its replacement of MSN Messenger), it will likely gain more traction.
Skype
Skype continues to be one of the most popular softphone applications in use today. Skype’s 300+ million users generate around two billion minutes a day. Skype has become one of the largest voice service providers in the world, estimated to be carrying some 25 percent of the global voice traffic. Skype utilizes a proprietary cloud-based client/server network to route calls online between users and has additional paid services allowing users to send calls to and receive calls from the public voice network. Microsoft acquired Skype in 2011. Microsoft used Skype to replace MSN Messenger in April 2013. Microsoft has also integrated Skype with Lync. One of the first released features from this union allows Skype and Lync “users around the world to connect over one communications platform.”5 Microsoft claims that many other innovations are in the works, with video chat being the next high-priority target for integration.
Architecture
In addition to the organizational changes with Skype, there have also been some architectural changes. Because of global crashes of the application, such as in 2010, Skype began moving away from the P2P super-nodes. The super-nodes were previously hosted on Skype users’ systems that could support the traffic based on bandwidth and processing capabilities. Skype has now created thousands of cloud-based super-nodes hosted by Microsoft in their data centers. These super-nodes reside on hardened Linux boxes using gresecurity, as indicated in an Ars Technica article.6
Network and Bandwidth Requirements
According to Skype’s own documentation, the minimum requirements for network access involve opening up TCP port access to all destination ports greater than 1024 (or, instead, to destination ports 80 and 443). A typical Skype connection will consume a minimum of 30 Kbps of bandwidth for a simple phone call and up to 8 Mbps for a group video call of seven or more people.
Blocking and Rate Limiting Skype in the Enterprise
Unauthorized enterprise use of Skype is a challenge for enterprise network administrators. This is a direct result of needing to limit the amount of bandwidth that Skype consumes and preserve bandwidth for critical programs. As you learned in Chapter 12, there are a variety of rate-shaping and Quality of Service technologies that aim to help tame the bandwidth utilization in your organization.
Skype traffic is difficult to detect and block because of the amount of encryption and network obfuscation used. A few solutions from traditional firewall and rate-shaping vendors purport to detect the latest versions of Skype. SonicWall, Checkpoint, and Cisco have features in their firewalls that allow Skype filtering. Solutions such as Blue Coat also claim Skype detection and throttling support, as do many intrusion prevention vendors. The only sure-fire way to block Skype from an enterprise perspective is to prevent its installation from a host-based policy-enforcement approach.
Security
Skype has maintained the appearance of ensuring the privacy of traffic within its network. However, in 2013, leaks from former NSA contractor Edward Snowden have indicated otherwise. In 2008, a small group of Skype managers embarked on “Project Chess,” which was intended to find “potential ways to increase government and law enforcement access to its VoIP calling service, years in advance of Microsoft’s acquisition in 2011” in order to cooperate with governmental agencies.7,8
When Skype changed its architecture from the P2P-based systems to cloud-based servers, this was touted as a means to combat recent global outages. One of the unmentioned additional features from the upgrade was the ability to intercept communications. With the new cloud-based architecture, it was much easier to break the encryption than with the previous P2P architecture. Other documents leaked by Snowden indicated that Skype joined PRISM in 2011 before Microsoft’s acquisition and after changes to the cloud-based architecture.9–14
Skype’s proprietary encryption makes it a perfect candidate for a covert tunnel. Simply put, outside of the NSA, you cannot decrypt the data to apply policy. There are multiple freely downloadable tools to establish a covert tunnel over Skype that can permit exfiltrating data completely undetected out of an enterprise that permits Skype usage. These tools can also be used to move malicious software into the environment, and one tool provides VNC remote capability. Many choose Skype as a lower-cost alternative without considering the risks.
Mobility and Smartphones
Mobility and smartphones (and tablets) allow users to constantly stay connected and communicate. Communication in this context can consist of voice, video, text messaging, messaging, and social networking (we cover these in more detail in the next section). What mobility and smartphones have enabled is the ability to constantly communicate through devices you always have with you. Our smartphones (and tablets) have essentially become part of our anatomy, and it is rare that we are without them. This has been a key driver in making all of the forms of communications so common. In fact, the term “smartphone” is really a misnomer—these devices are really very powerful computers, with large high-resolution touch screens, great user interfaces, and constant access to the Internet via cellular (3G, 4G, and LTE) or Wi-Fi. Interestingly, the voice application is becoming a neglected application on many smartphones, at least for consumers and young people.
Smartphones and tablets are heavily used within the enterprise. Whether provided by the user or enterprise, smartphones (and tablets) are increasingly vital in many jobs. As an example, voice communications using smartphones is increasing in the enterprise. This is especially true for our progressively mobile and telecommuting workforce, who aren’t always by their desk phone. Other applications are used as well, especially when the device is used for both personal and enterprise purposes, which we cover in the “Bring Your Own Device (BYOD)” section.
Security
Smartphones can get malware and viruses the same way PCs can, but it is much less common. In the past, the incentive for infecting a smartphone was lower because there wasn’t that much interesting data there, but this has changed with smartphones being used for so much, including financial transactions and enterprise use.
One attack affecting text messaging occurs when a piece of malware is installed on a user’s smartphone, usually an Android-based device, which, in turn, generates many text messages to premium numbers. This is similar to the IRSF-based toll fraud attacks covered in Chapter 5, but applied to smartphones and text messaging. Basically, the piece of malware, at some interval and frequency, runs and generates the premium text messages. In some cases, the malware can also receive return responses (say, for a purchasing a custom ring tone), block delivery to the user, and confirm the charge.15
A fraud attack may be a consumer or enterprise issue, depending on who is paying for the service. In a BYOD situation, which we discuss later, the enterprise often pays for much of the voice and data access for the smartphone. As such, any abuse will be an issue for the enterprise.
Although it has not occurred yet, it is possible for a piece of malware to run on a smartphone and make calls to IRSF numbers at night or some time when the user would not notice. If an attack such as this could, say, run every night for a month and the user did not notice, they or the enterprise could get stuck for a significant bill. Fortunately, the voice application is usually locked down tightly for some devices, such as iOS and probably Android in the future, making this attack difficult to execute.
We are also seeing an increase in robocalls targeting smartphones (our mobile numbers). These calls fall into the categories of voice SPAM and voice phishing. Historically, these calls were less frequent because attackers could be fined for calling cell phones (because the calls cost money) and the numbers were more difficult to get. This has changed, and in reality smartphone numbers are often better targets because more residential users are dropping their home phones or at least ignoring most of the calls.
In the past, Android offered a number of applications that helped to block these robocalls. The applications could block the calls and used crowdsourcing to build effective databases of blacklisted numbers. There are multiple applications, one of which is Mr. Number (www.mrnumber.com). Figure 17-4 shows the website.
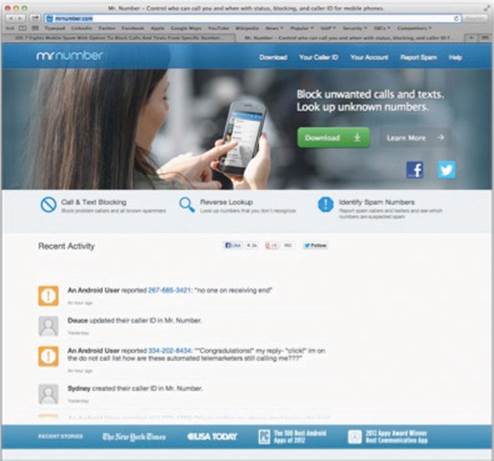
Figure 17-4 Mr. Number website
Android is moving to a model where the voice application is tightly controlled, so these applications may not work in the future. These capabilities are not available for Apple iOS, where the cellular voice application is locked down. Apple iOS 7.0 has integrated some basic blocking capability.16,17
Note![]()
Some applications claim to provide the ability to block robocalls (and texts). However, most don’t work and are a waste of time.18
Another possible attack against smartphones and tablets is to intercept the cellular traffic itself. Devices are available that can intercept GSM, CDMA, and other cellular protocols. This includes femtocell (microcell) technology, which allows an attacker to set up their own cellular capability and intercept traffic.19–21
Other Forms of Communications
Users now connect more frequently with forms of communication other than voice. Although not new, mobility, smartphones, tablets, and other technologies have made it easy and convenient to use video, text, instant messages, and social networking. Cloud services and constant access to the Internet also help to make this possible. Many of us send hundreds of messages a day, while only making a handful of voice calls. This is especially true for consumers and the younger generation, who might send thousands of messages, post text and pictures via social networking, and maybe make an occasional voice call. We cover some of these technologies in the next several sections.
Video
We have mentioned video throughout the book and covered it extensively in Chapter 16. Enterprise video, in the form of high-end TelePresence, video-enabled desktop phones, UC applications, or public cloud conferencing services such as Cisco Webex, is seeing wider adoption. Consumer-oriented video, including video chat within UC applications such as Skype, iPhone’s FaceTime, Whatsapp, or one of the UC applications mentioned in this chapter, is also being used more.
All video calls include an audio component. Any video call can have its audio component attacked, independent of the actual video. The actual video leverages the same signaling protocol, such as SIP, and now there is more data or streams for the actual video. RTP remains a common way of exchanging the actual video data, the main differences being packet volume and codec.
The future of video is unknown. Video is becoming easier to use and networks have more bandwidth to accommodate it. However, at the same time, other forms of communication, such as text messages, instant messages, and social networking, are increasing in use. People take videos and post them as well as watch Internet-based videos for entertainment and training, but taking the time to sit down and have a high-quality video conversation is not as common. Video is great for users needing a high-fidelity conversation, such as for a key business meeting, seeing a loved one who is overseas, seeing the children while on a business trip, letting the grandparents see the new baby, and so on, but these types of communications represent a small fraction of the overall conversations.
Security
The security issues with video were well documented in Chapter 16. Generally, any attack that works against voice will work against video. Any system that uses RTP for the actual video will be susceptible to attacks against that protocol. Any video will be susceptible to attacks that degrade its quality (although choppy video is still tolerated). Attacks against video get more difficult when the data is encrypted, however.
Text Messaging
Text messaging—more appropriately called the Short Message Service (SMS)—has been around for many years and is actually tied to the voice network. Everyone is familiar with text messaging; it is available on virtually every mobile phone, even old feature phones. Text messaging used to be expensive, but the cost has come down, and unlimited texting plans are very common. Text messaging, although not as elegant as instant messaging (covered later), has the benefit of being ubiquitously available. Pretty much anyone with a cell phone can send and receive text messages, as opposed to Internet messaging clients, which requires an application and they usually don’t federate with one another.
Text messaging has the huge advantage over voice in that you can reach multiple people at one time (group messages); you can maintain multiple conversations at one time (be careful and don’t mix up the recipients’ messages); and you can have a conversation with someone who is busy and can’t have a voice conversation. Text messaging has sort of become the mode of communication that works when all else fails. Maybe your target can’t take a call. Maybe they are in a meeting or with someone who won’t like you calling them. Maybe they are somewhere very loud. Maybe they aren’t running their favorite messaging client right now. It is pretty much a given that they will have their smartphone and can check it. In some cases this behavior is rude, but it is so common that it has become more accepted, as long as you don’t start a long text conversation with someone.
Security
Some of the attacks covered in Part II do affect text messaging. We are seeing more text-message-based voice SPAM (SPIM) and voice phishing (smishing). It is possible to determine the area code and prefix used by the major cellular phone providers, so it is easy to get target phone numbers. A number of resources on the Internet can help you find the area codes and prefixes used by mobile providers and to confirm that a number is indeed a mobile number. Figure 17-5 shows the site www.surfaceslikenew.com, which is rather handy for these purposes.
Figure 17-5 Surfaces Like New cell phone website
Other sites that will let you know what type of phone a number is associated with are www.whitepages.com/reverse_phone and www.searchbug.com/tools/landline-or-cellphone.aspx.
If you are trying to leave a message and get a user to call you back for some product, service, or scam, text messaging is a great mechanism, because most users will check their text messages. It is also effective to leave a message and number if you are trying to get the user to call a number and leave personal information. These attacks are really targeted at consumers but affect enterprise users as well because the attacker can’t really tell where the target cell phone is being used. The article “Two-thirds of Mobile Phone Users Get SMS Spam” provides some metrics for SPIM and smishing.22 Figure 17-6 shows an actual smishing text that one of us just received.
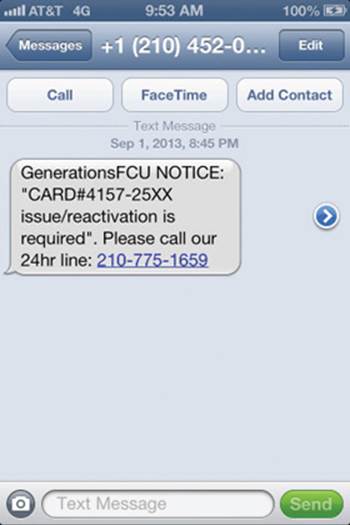
Figure 17-6 Example of smishing message
A number of the messaging services (covered next) are described as “text messaging” replacement services and offer free integration with text messaging. These systems can also be used to originate text messages. The commercial robodialing companies, including Call-Em All (www.call-em-all.com), also offer the ability to generate text messages. There are also ways to send emails that get converted to text messages. One service that offers this capability can be found at www.makeuseof.com/tag/email-to-sms/. The commercial calling number spoofing services, such as SpoofCard (www.spoofcard.com), can also generate text messages with spoofed source numbers. This can be useful for smishing and spear smishing attacks.
Sending many text messages to a smartphone without an unlimited plan will cost the user money. This is a form of fraud that is seen from time to time.
Messaging
In addition to text messaging, users can use a variety of applications that exchange short or “instant” messages. The idea is the same as text messages, but the user employs an application and the Internet rather than the voice network. Messaging is not new—these applications have been around for many years, but with mobility and smartphones, the ability to stay connected and constantly send messages is increasing. Messaging continues to grow in enterprises, with both public cloud-based offerings as well as enterprise-class systems from vendors such as Cisco and Microsoft.
Messaging introduced the concepts of “presence” and “buddy lists,” where you connect only with your contacts. This allows you to see their current status or presence indicating whether they are available to chat. This makes communication much easier because there is no need to try to chat with someone who is not online or busy. Presence can be applied to any form of communications and makes any real-time contact much more efficient. Messaging introduced other common features, such as when a message was delivered, when a message was delivered read, when the other person is typing, and so on. It also introduced the use of various shorthands, such as the famous IMHO, LOL, and OMG, as well as the use of emoticons, or icons that indicate happiness, sadness, or anger.
There is a long list of messaging applications. Most of these applications also offer the ability to make voice and video calls. Here are some of the most common ones:

Some of these applications are designed exclusively for smartphones, whereas others support smartphones as well and PCs, Macs, and more. Many of the early messaging applications have faded away, have been merged into new systems, or have more limited use (for example, Yahoo! Messenger). Some applications, such as iMessage, are very popular, but only run on iOS or a Mac. These applications are heavily used by consumers but are also making their way into enterprises. These devices are often used within the enterprise as part of a BYOD initiative, which means they may be used for enterprise work or have some data exchanged that should not be exchanged.
Some of these applications bill themselves as text messaging replacements, allowing messages to be sent without incurring text message charges. Of course, you as well as your friends have to have the application for this to work. Some of these services offer free hop off to text messaging as well.
Security
Messaging security issues have become pretty well known. Use of messaging implies that the user has installed an application on their PC, Mac, tablet, or smartphone, any of which can be used for enterprise work. Because this application is directly connected to the Internet, a vulnerability could be exploited to gain access to the system. Messaging applications usually allow for the downloading of files, which could contain malware. Instant messaging also offers another way to send communication or files out of the enterprise, thus creating a data leakage/loss issue. Attacks such as toll fraud, harassing calls, and TDoS, voice SPAM, and voice phishing really don’t affect messaging applications too much, because they are generally closed systems and most of your communications are with your contacts. However, these sorts of attacks are being seen in very large systems such as Skype.
Most of these applications use encryption to protect the communications exchange. How strong the encryption is varies from application to application.
Enterprise Messaging
Enterprises are adopting presence and messaging—some through consumer offerings, but also with enterprise-class offerings from vendors such as Cisco, Microsoft, and many others. We covered Microsoft Lync earlier. Their offering has the advantage of keeping local messages within the enterprise. They have a full-featured messaging (and presence, voice, and video) client. Figure 17-7 provides a view of this client.
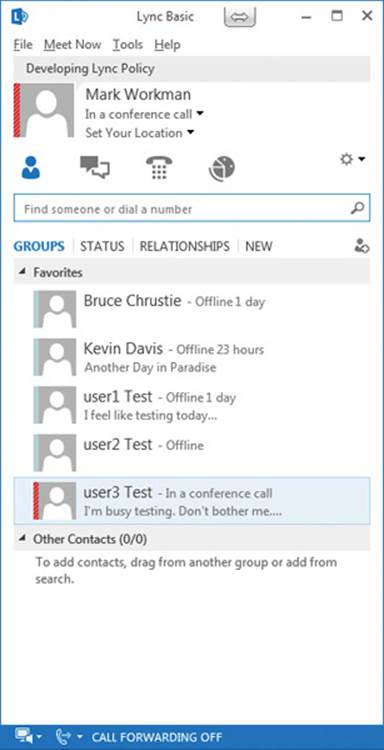
Figure 17-7 Microsoft Lync client
Cisco acquired Jabber, an open standards-based messaging system, in 2008. Like Microsoft, Cisco Jabber supports presence, messaging, voice, and video calling. Jabber can use the Webex Connect server in the public cloud or Cisco’s Unified Presence (CUP) service, which has the advantage that internal messages are not sent out to the cloud. Jabber communications can be encrypted. A sample screenshot of the Jabber client is shown in Figure 17-8.
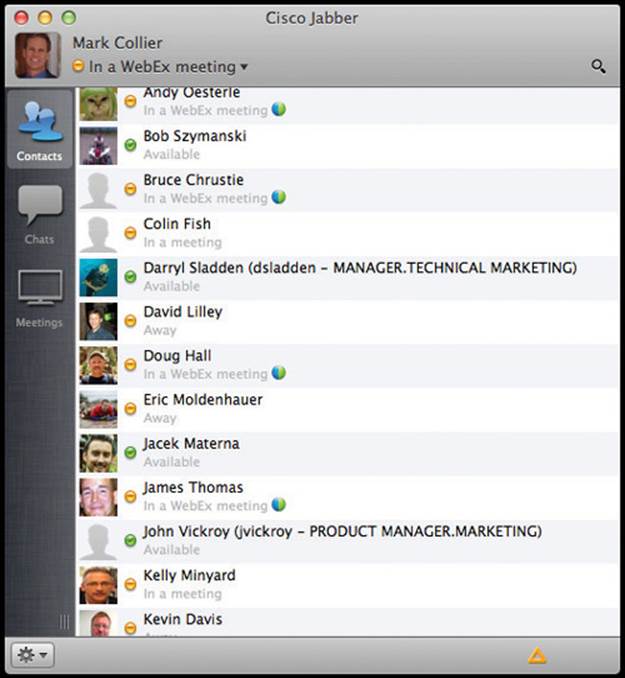
Figure 17-8 Jabber client
Security
The security issues for enterprise messaging systems are similar to those for the public cloud messaging systems. However, these systems offer the advantage of keeping the message flow within the enterprise. These systems also offer encryption, which because it is in the control of a more known vendor, is arguably better. Microsoft, by default, encrypts all communications to and from their client.
Social Networking
Social networking sites such as Facebook, LinkedIn, Twitter, Instagram, Snapchat, Google+, and so on, are used heavily for communications. Some of these systems have built-in messaging capabilities, including Facebook and LinkedIn, but most of the communication comes in the form of brief messages, status updates, pictures, and videos. Users also “communicate” by “liking,” commenting on, and redistributing status updates, pictures, and so on, that they like. One might argue that this isn’t necessarily traditional communication, but it is very pervasive, especially with the proliferation of smartphones. Users are constantly “tweeting,” updating their status on Facebook and LinkedIn, posting pictures on Instagram, Facebook, and Snapchat, and posting short videos on Instagram and Vine. Each of these social networking sites has a slightly different model, but all include the idea of friends, contacts, and so on.
Enterprise users make heavy use of LinkedIn for professional networking. Many businesses use Twitter, Facebook, and LinkedIn to communicate updates, marketing information, and so on. Having an enterprise presence on Facebook, Twitter, and LinkedIn is pretty much a requirement. Many small enterprises don’t even have websites anymore—just Facebook and other social networking site presences. Some enterprises are using Facebook, as an example, for internal collaboration and communications. Some vendors, such as Cisco, Microsoft, Salesforce, and IBM, offer enterprise-class social networking and collaboration systems, but in our opinion, they have not been adopted as rapidly as the vendors had hoped—and, of course, nothing like the adoption level for consumers.23,24
Security
The security issues for social networking are well known. These sites are designed for public networking and, by their very nature, err on the side of giving out information rather than keeping it private. These are all public cloud services, so all of your data is outside of your control. Be very cautious about using any of these services for sensitive data. The enterprise-class offerings have the advantage of being internal and protecting data, but, again, their adoption has been limited.
Bring Your Own Device (BYOD)
In the past, users would have to use their personal smartphone and then some device provided by the enterprise, such as a Blackberry for email. This has changed, and most enterprises have adopted a bring-your-own-device (BYOD) policy. This allows the user to bring in their favorite smartphone, tablet, and even computing platform (such as a Mac), with the enterprise IT now agreeing to support it. This is a big benefit to the user because they get to use one familiar device of their choosing, and it has become the model for many enterprises.
Security
BYOD can expose critical enterprise data (including, at a minimum, emails) to the applications and activities on the consumer side of the smartphone. The enterprise also has to grant network Wi-Fi access to the device while in use at the enterprise site. This is a benefit to the user, but creates many security issues, because the user’s consumer-side habits and applications blend with those of the enterprise, creating security and exchange-of-data risks. The smartphone will have critical enterprise data on it, emails, messages, data from applications, and files, which may get accessed from attacks that originate on the consumer side. The user may also be careless about protecting the data, even to the point of losing the device, where a thief could potentially access all the data on the smartphone. Many resources are available that cover this aspect of smartphone security, and some companies provide mobile device management (MDM) designed to maintain data separation, remotely wipe the device if it is lost, and so on.
As described earlier, the cost of any toll fraud attack on the smartphone is likely to be covered by the enterprise.
The Cloud
Another factor is the continued migration of UC to “the cloud,” which is a new computing model where computing and networking are elastic and flexible, as opposed to a model where you have to add a server or PC every time you need more power. Cloud computing can be private (in an enterprise data center) or public (off premises in some provider’s facility). Generally when people think of the cloud, they think of the public model, where the computer, infrastructure, applications, and data are off premises. We use this model constantly, through major providers such as Google, Amazon, Yahoo!, and Facebook. Also, most all of the messaging, social, voice, and video applications we covered are hosted in the cloud. The intelligence for mobility and cellular services is also in the cloud. And, of course, long-distance and international voice have always been in the cloud.
Although enterprises have historically maintained their own PBXs and applications, voice has always used a hybrid model leveraging the cloud. Switches and applications have always been in the service provider’s cloud to provide the public voice network services. This model adoption is accelerating, where more of the voice and UC intelligence is available via the cloud. Even with PBXs, any calls offsite (long distance or international) go through a service provider cloud.
Consumers have become very comfortable with their personal communications occurring over the cloud, as they have little choice. Although the enterprise has been slower to adopt some of these services, this is changing. There has been a shift of critical enterprise communications to mobile, messaging, OTT applications, social, and so on.
Hosted UC
Another benefit to the cloud is that service providers are offering more ability to host and manage key enterprise UC applications. Enterprises are more likely to move critical applications, including the IP PBX and contact center software, especially an IVR, to the cloud. VoIP makes this so much easier than in the traditional Centrex model, where you had to have a dedicated wire set to each and every phone. You still need phones, softphones, or end-user applications, but moving UC intelligence to the cloud is getting increasingly easily. Enterprises are already moving it to their private cloud in data centers, but also to the public cloud. Service providers and other companies are offering hosted IP, hosted VoIP, and UC as a Service (UCaaS), where they control and manage all the hardware and applications, and the enterprise only has the phones and client applications. Some vendors simply host enterprise-class UC systems from Cisco, Microsoft, and Avaya, whereas others have built their own enterprise-class systems, such as 8x8 (www.8x8.com). These services allow the enterprise to avoid an upfront capital purchase, eliminate the management and security hassles of setting up and maintaining a system, and are paid with a monthly fee. These vendors are especially attractive to small enterprises that don’t want to set up their own system. They are increasingly attractive to large enterprises as well, especially for specialized applications such as IVRs.
Security
The main security issue for the cloud is that you must trust the provider with all your applications and data. Google knows all your search terms and probably knows you better than you do. All your personal information, photos, and such are on Facebook and Instagram servers. If you use Amazon or Rackspace to host applications, your data is in their cloud as well. All your communications via text messaging, for example, go through the provider’s system, network, and applications. Even if the application you use supports encryption, which may thwart some unscrupulous ISP or other person in the middle, it won’t stop the provider who manages the system. Take Skype, for example: although it uses strong encryption, it runs through servers controlled by Microsoft. The same is true for Apple’s iMessage. Text messaging isn’t usually encrypted, so it is wide open. You not only have to trust the service provider with your data, but you also must trust that they will secure their systems adequately so as not to be attacked themselves.
Cloud-based services require a robust Internet connection. Any attack that compromises or disrupts this connection will affect the cloud service.
WebRTC
Web Real-time Communications (WebRTC), which defines all the capability you need to make voice and video calls from within your browser, is an evolving standard being defined within the IETF and W3C. So now, rather than using an external application such as Skype to make calls, the same software is built into the browser so you do not need an extra application. If you want to add a “click to call” button, for example, everything you need to make the call is built in—you don’t have to launch an external application. Furthermore, WebRTC will be a standard, so a call originating from one browser should be fully compatible with a call from another browser. This is a big advantage over closed systems such as Skype, Viber, Line, and Whatsapp, where you are calling from within their application and there is little, if any, federation. With WebRTC, anyone can call anyone.
WebRTC is currently supported within the Google Chrome and Mozilla Firefox browsers. Microsoft Internet Explorer and Apple Safari do not support it yet, but hopefully this will change in the near future.
There is a huge amount of “buzz” around WebRTC and a long list of resources, articles, and conferences. The following are several good introductory resources:

Security
WebRTC is being designed with security built in.25,26 The RTP is always encrypted with SRTP and DTLS (SDES was considered, but DTLS was agreed upon). The signaling will be encrypted through HTTPS.
Because WebRTC provides APIs to turn on the microphone and camera, it will be possible for malicious software on a website to activate these resources. Basically you could access a website and the software could listen to your voice or watch your video without your knowledge.
Just like when you receive advertisements when you access a website, you may now get a phone call. Also, assuming WebRTC catches on, there will certainly be opportunities for application-level attacks, such as voice SPAM, voice phishing, and possibly TDoS.
Summary
Unified Communications (UC) is in a constant state of change. Legacy voice has largely migrated to VoIP. VoIP has expanded to UC, which brings in new communication types, including video, presence, messaging, and social networking. Major new players in this market, including Microsoft, have offerings that are inherently UC based. We expect Microsoft to gain market share in the future. UC is also changing due to the capability of smartphones and tablets, where consumers and enterprise users are constantly connected to the Internet and always able to communicate. Communication is changing, because although voice still has a huge role, especially in the enterprise and contact centers, many conversations are replaced by simple text messaging, social networking posts, and so on. Many voice calls occur on smartphones rather than traditional desk sets. OTT voice, such as Skype, is also being used more in the enterprise. All the while, more and more of the enterprise communication’s intelligence has left the premises and is moving to the public cloud. Finally, some new protocols such as WebRTC offer the promise of standardizing Internet-based voice and building it right into the web browser.
References
1. Microsoft Lync reference diagrams, http://technet.microsoft.com/en-us/library/gg398254.aspx.
2. Microsoft Security Advisories, www.microsoft.com/technet/security/current.aspx.
3. Unified Communications Strategies, “MS Office, Lync Vulnerabilities Can Be Exploited by Attackers to Control Infected Systems,” www.ucstrategies.com/unified-communications-newsroom/ms-office-lync-vulnerabilities-can-be-exploited-by-attackers-to-control-infected-systems.aspx.
4. Creating Outgoing Dialers with UCMA 3.0, http://msdn.microsoft.com/en-us/library/lync/hh530044(v=office.14).aspx.
5. Emil Protalinski, “Microsoft Completes Lync Integration into Skype, Offers One Unified Communications Platform for Windows and Mac,” TNW, http://thenextweb.com/microsoft/2013/05/29/microsoft-completes-integration-of-lync-and-skype-finally-offers-one-unified-communications-platform/.
6. Dan Goodin, “Skype Replaces P2P Supernodes with Linux Boxes Hosted by Microsoft (updated),” ArsTechnica, http://arstechnica.com/business/2012/05/skype-replaces-p2p-supernodes-with-linux-boxes-hosted-by-microsoft/.
7. Chris Davies, “Skype Project Chess Allegedly Explored NSA Access Ahead of Microsoft Buy,” SlashGear, www.slashgear.com/skype-project-chess-allegedly-explored-nsa-access-ahead-of-microsoft-buy-20287207.
8. Ryan Gallagher, “Report: Skype Formed Secret ‘Project Chess’ to Make Chats Available to Government,” Slate, www.slate.com/blogs/future_tense/2013/06/20/project_chess_report_says_skype_worked_on_secret_project_to_provide_chats.html.
9. James Risen and Nick Wingfield, “Web’s Reach Binds N.S.A. and Silicon Valley Leaders,” The New York Times, www.nytimes.com/2013/06/20/technology/silicon-valley-and-spy-agency-bound-by-strengthening-web.html?_r=0.
10. Chris Davies, “Microsoft Unlocked Skype Chat Backdoor Tip Insiders,” SlashGear, www.slashgear.com/microsoft-unlocked-skype-chat-backdoor-tip-insiders-26240382/.
11. Nick Statt, “Skype: Reportedly Funneling Your Calls to PRISM Since 2011,” readwrite, http://readwrite.com/2013/07/11/skype-has-been-funneling-your-audio-and-video-calls-to-prism-for-two-years#awesm=~ohlnMhVLfdveBM.
12. Dan Goodin, “Think Your Skype Messages Get End-to-End Encryption? Think Again,” ArsTechnica, http://arstechnica.com/security/2013/05/think-your-skype-messages-get-end-to-end-encryption-think-again/.
13. Glen Greenwald, “Microsoft Handed the NSA Access to Encrypted Messages,” The Guardian, www.theguardian.com/world/2013/jul/11/microsoft-nsa-collaboration-user-data.
14. PRISM (surveillance program), Wikipedia, http://en.wikipedia.org/wiki/PRISM_%28surveillance_program%29.
15. Meghan Kelly, “Toll Fraud: Lurking Thieves Steal Money Through Your Texts,” VB, http://venturebeat.com/2012/09/06/toll-fraud-lookout-mobile/.
16. Josh Constine, “iOS 7 Fights Mobile Spam with Option to Block Calls and Texts from Specific Numbers,” TechCrunch, http://techcrunch.com/2013/06/10/ios-call-blocking/.
17. Rene Ritchie, “iOS 7 Preview: Phone, FaceTime, and Messages Blocking Promises to Put an End to Annoying Contacts,” iMore, http://www.imore.com/ios-7-preview-phone-facetime-and-messages-blocking.
18. John Matarese, “Apps to Block Cell Phone Robocalls—Don’t Waste Your Money,” ABC News, www.abc2news.com/dpp/money/consumer/dont_waste_your_money/Copy_of_apps-to-block-cell-phone-robocalls1376492737330.
19. Andrew Couts, “Meet the $250 Verizon Device that Lets Hackers Take Over Your Phone,” Digital Trends, www.digitaltrends.com/mobile/femtocell-verizon-hack/.
20. Fahmida Rashid, “Black Hat: Intercepting Calls and Cloning Phones with femtocells,” PC Magazine, http://securitywatch.pcmag.com/hacking/314370-black-hat-intercepting-calls-and-cloning-phones-with-femtocells.
21. Sebastian Anthony, “4G and CMDA Reportedly Hacked at DEFCON,” ExtremeTech, www.extremetech.com/computing/92370-4g-and-cdma-reportedly-hacked-at-def-con.
22. Fred Donovan, “Two-thirds of Mobile Phone Users Get SMS Spam,” Fierce Mobile IT, www.fiercemobileit.com/story/two-thirds-mobile-phone-users-get-sms-spam/2013-08-17?utm_campaign=TwitterEditor-FierceCIO.
23. Irwin Lazar, “The State of Enterprise Social,” Nemertes Research, https://www.nemertes.com/blog/state-enterprise-social.
24. Matt Rosoff, “LinkedIn CEO on Competing with Yammer or Chatter,” CITEworld, www.citeworld.com/social/22386/linkedin-jeff-weiner-enterprise-social.
25. Eric Rescorla, “Proposed WebRTC Security Model,” http://www.ietf.org/proceedings/82/slides/rtcweb-13.pdf.
26. Eric Rescorla, “Security Considerations for WebRTC,” http://tools.ietf.org/html/draft-ietf-rtcweb-security-05.
All materials on the site are licensed Creative Commons Attribution-Sharealike 3.0 Unported CC BY-SA 3.0 & GNU Free Documentation License (GFDL)
If you are the copyright holder of any material contained on our site and intend to remove it, please contact our site administrator for approval.
© 2016-2026 All site design rights belong to S.Y.A.