Hacking Exposed 7: Network Security Secrets and Solutions (2012)
INTRODUCTION
“RISE AND RISE AGAIN, UNTIL LAMBS BECOME LIONS.”
This quote from Russell Crowe’s 2010 movie Robin Hood, provides no more important sound bite for this Seventh Edition of Hacking Exposed™. Make no mistake, today we are the lambs—being offered up for slaughter every minute of every day. But this cannot continue. We cannot allow it. The consequences are too dire. They are catastrophic.
We implore you to read every word on every page and take this warning seriously. We must understand how the bad guys work and employ the countermeasures written in these pages (and more), or we will continue to be slaughtered and our future supremely compromised until we do.
What This Book Covers
While we have trimmed and expanded all the content in this book, we need to highlight a few brand new areas that are of critical importance. First, we have addressed the growing attacks surrounding APTs, or Advanced Persistent Threats, and given real-world examples of how they have been successful and the ways to detect and stop them. Second, we have added a whole new section exposing the world of embedded hacking, including techniques used by the bad guys to strip a circuit board of all its chips, reverse engineer them, and determine the Achilles heel in the dizzying world of 1s and 0s. Third, we’ve added an entire section on database hacking, discussing the targets and the techniques used to pilfer your sensitive data. Fourth, we dedicated an entire chapter to mobile devices, exposing the embedded world of tablets, smartphones, and mobility, and how the bad guys are targeting this exploding new surface area. And finally, something we should have done from the very first edition in 1999, we’ve added a dedicated chapter on countermeasures. Here, we take an expansive role in explaining the world of what you, the administrator or end user, can do to prevent the bad guys from getting in from the start.
How to Use This Book
The purpose of this book is to expose you to the world of hackers, how they think and work. But it is also equally purposed to educate you on the ways to stop them. Use this book as the definitive source for both of those purposes.
How This Book Is Organized
In the first part “Casing the Establishment,” we discuss how hackers learn about their targets. They often take meticulous steps to understand and enumerate their targets completely, and we expose the truth behind their techniques. In the second part “System Hacking,” we jump right in and expose the ultimate goal of any savvy hacker, the end desktop or server, including the new chapter on APTs. The third part, “Infrastructure Hacking” discusses the ways bad guys attack the very highway that our systems connect to. This section includes the new material on hacking embedded systems. The fourth part, “Application and Data Hacking” discusses both the web/database world as well as mobile hacking opportunities. This part is also where we discuss countermeasures that can be used across the board.
Navigation
Once again, we have used the popular Hacking Exposed™ format for the Seventh Edition; every attack technique is highlighted in the margin like this:
![]() This Is the Attack Icon
This Is the Attack Icon
Making it easy to identify specific penetration tools and methodologies. Every attack is countered with practical, relevant, field-tested workarounds, which have a special Countermeasure icon.
![]() This Is the Countermeasure Icon
This Is the Countermeasure Icon
Get right to fixing the problem and keeping the attackers out.
Pay special attention to highlighted user input as bold in the code listings.
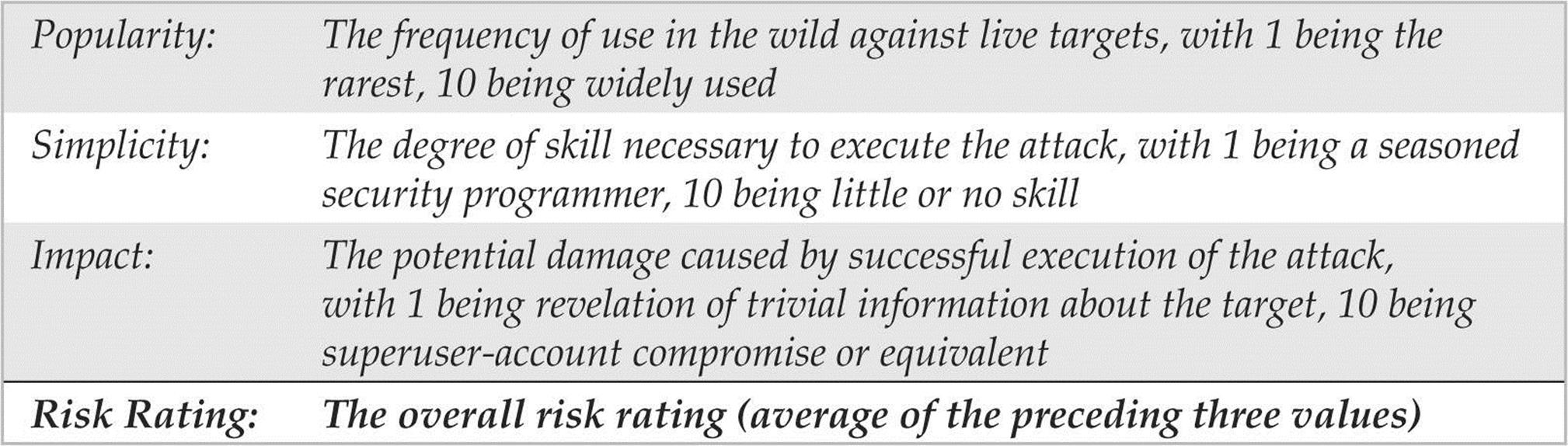
Every attack is accompanied by an updated Risk Rating derived from three components based on the authors’ combined experience.
All materials on the site are licensed Creative Commons Attribution-Sharealike 3.0 Unported CC BY-SA 3.0 & GNU Free Documentation License (GFDL)
If you are the copyright holder of any material contained on our site and intend to remove it, please contact our site administrator for approval.
© 2016-2026 All site design rights belong to S.Y.A.