Introduction To Network Security: Theory And Practice (2015)
Chapter 1. Network Security Overview
1.2 Common Attacks and Defense Mechanisms
Common network security attacks can be characterized into a few basic types. Almost every known network security attack is either one of these basic types or a combination of several basic types.
1.2.1 Eavesdropping
Eavesdropping is an old and effective method for stealing private information. In network communications, the eavesdroppers may intercept data from network traffic using a networking device and a packet sniffer. A packet sniffer, or network sniffer, is a program for monitoring incoming network traffic. When connecting a router to the Internet, for example, one can use a packet sniffer to capture all the IP packets going through that router. TCPdump and Wireshark (formerly known as Ethereal) are network sniffers widely used today, which are available as free downloads (see Exercise 1.5).
Using a packet sniffer as an eavesdropping tool, one can intercept IP packets that go through the router he controls. To capture a particular IP packet, however, the eavesdropper must first determine which communication path the IP packet will travel through. Then, he could either try to get control of a certain router on the path or try to insert a new router of his own on the path. This task is more difficult but is not impossible. For example, the eavesdropper may try to compromise a router on the path and install a packet sniffer in it to intercept the IP packets he is after. The eavesdropper may also use an ARP spoofing technique (see Section 1.2.4) to reroute IP packets to his sniffer without compromising a router.
Eavesdropping wireless communications is easier. In this case, the attacker simply needs to place a receiver with the same radio frequency of the wireless network within the communication range of the network.
There is no way to stop eavesdropping in public networks. To counter eavesdropping, the best defense mechanism is to encrypt data. Computer cryptography is developed for this purpose, where the sender encrypts data into an unintelligible form before he transmits it. Data encryption is a major component of computer cryptography. It uses an encryption key in concert with an encryption algorithm, to break the original data into pieces and mix them up in a certain way to make it unintelligible, so that the eavesdropper cannot obtain any useful information out of it. Thus, even if the eavesdropper is able to intercept the encrypted data, he is still not able to obtain the original data without knowing the decryption key. We often refer the original data as plaintext data, or simply plaintext, and encrypted data as ciphertext data, or simply ciphertext.
Ciphertext data can be converted back to plaintext data using a decryption key along with a decryption algorithm. The encryption key is a string of characters, which is also referred to as secret key. In a symmetric-key encryption algorithm, also referred to as conventional encryption, the encryption key and the decryption key are identical. In a public-key encryption algorithm, also known as asymmetric-key encryption, the encryption key and the decryption key are different.
1.2.2 Cryptanalysis
Cryptanalysis is the art and science of finding useful information from ciphertext data without knowing the decryption keys. For example, in a substitution cipher that substitutes plaintext letters with ciphertext letters, if a ciphertext message reveals a certain statistical structure, then one may be able to decipher it. To obtain a statistical structure of the data, one may calculate the frequency of each character in the ciphertext data and compare it against the known statistical frequency of each character in the language used in the plain text. For example, in the English language, the letter “e” has the highest frequency. Thus, in a substitution cipher, the character that has the highestfrequency in the ciphertext data is likely to correspond to the plaintext letter “e” (see e.g., Exercise 1.7). This analysis can be further extended to common phrases. Analyzing statistical structures of ciphertext messages was an effective method to break encryptions before the computer era.
Modern encryption algorithms can produce ciphertext without any trace of statistical structure. Therefore, modern cryptanalysis is focused on analyzing encryption algorithms using mathematical techniques and high-performance computers.
The best method against cryptanalysis is to devise encryption algorithms that reveal no statistical structures in ciphertext messages using sophisticated mathematics and longer encryption keys. Using sophisticated mathematics makes mathematical analysis difficult. Using longer keys makes brute force attacks impractical. In addition to having stronger encryption algorithms, it is equally important to distribute and manage keys safely and to implement encryption algorithms without exploitable loopholes.
1.2.3 Password Pilfering
Computer users need to prove to the system that they are legitimate users. The most widely used authentication mechanism is in the form of user names and user passwords. User names are public information, but user passwords must be kept secret. Only two parties should have knowledge of the password, namely, the user and the underlying computer program (e.g., an operating system or a specific software application). A password is a sequence of letters, digits, or other characters, which is often selected by the user. Legitimate users enter their user names and passwords to prove their legitimacy to the computer program. An unauthorized user may impersonate a legitimate user to “legitimately” log on to a password-protected system or application, if he can get hold of a legitimate user name and password pair. He can then gain all the “legal” rights to transmit, receive, modify, and fabricate data.
Password protection is often the first defense line, and sometimes, it may be the only defense mechanism available in the system. Thus, we must take measures to ensure that user passwords are well protected against larcenies. For this purpose, we will look at several common methods for pilfering user passwords. These methods include guessing, social engineering, dictionary attacks, side-channel attacks, and password sniffing. Phishing attacks and pharming attacks have become the most common form of mass social engineering attacks in recent years.
1.2.3.1 Guessing
Guessing is the simplest method to acquire a password illegitimately. The attacker may get lucky if users use short passwords or if they forget to change the default passwords created for them. Also, users have a tendency to use the same passwords.
According to data compiled yearly by SplashData, a password management company, the top 10 most common passwords used by users, listed in decreasing order of popularity, are as follows:
1. 123456
2. password
3. 12345678
4. qwerty
5. abc123
6. 123456789
7. 111111
8. 1234567
9. iloveyou
10.adobe123
If the user chooses a simple password such as these 10 easy ones, then the guesser would indeed have an easy task.
1.2.3.2 Social Engineering
Social engineering is a method of using social skills to pilfer secret information from the victims. For example, attackers may try to impersonate people with authority or organizations of reputation to trick unvigilant users to reveal their usernames and user passwords to the attackers. Impersonation may be carried out either in person or in an electronic form. Phishing and pharming are common electronic forms of social engineering attacks in recent years, targeted at a large number of people.
There are other forms of social engineering attacks. For example, attackers may try to collect recycled papers from the recycle bins in a corporation's office building, hoping to find useful login information. Attackers may also make a Web browser pop up a window asking for user login information.
Physical Impersonation
Physical impersonation means that the attacker pretends to be a different person to delude the victim. For example, the following imaginary conversion between the attacker and a receptionist named Betty demonstrates how a social engineering attack might be carried out in person:
Attacker: (Speaking with an authoritative voice.) “Hello, Betty, this is Nina Hatcher. I am Marketing Manager of the China branch office.”
Betty: (Thinking that this woman knew my name, my number, and spoke like a manager, she must be whom she said she was.) “Hello, Nina, what can I do for you?”
Attacker: “Betty, I am attending a meeting in Guangzhou to finalize an important deal with a large corporation in China. To close the deal, I'll need to verify certain technical data produced by your group that I believe is still stored in the computer at your site. This is urgent. I tried to log on to your system today, but for some reason it didn't work. I was able to log on to it yesterday though. Is your computer down? Can you help me out here?”
Betty: “Well, I don't know what happened. But you may try the following ![]() ” (Thinking that she is doing the company a favor by telling the marketing manager how to get into the system.)
” (Thinking that she is doing the company a favor by telling the marketing manager how to get into the system.)
Phishing
Phishing attacks are mass social engineering attacks that take advantage of people with a tendency to trust authorities. The main forms of phishing attacks are disguised email messages or masqueraded Websites. For example, attackers (also called phishers) send disguised email messages to people as if these messages were from banks, credit card companies, or other financial institutions that people may pay attention to. People who receive such messages are told that there was a security breach in their accounts, and so they are required to verify their account information for security purposes. They are then directed to a masqueraded Website to enter their user names and passwords (e.g., see Exercise 1.15). The following example is a real phishing message verbatim (The reader may notice a number of grammatical errors and format problems.):
From: UML NEW EMAIL <helpdesk@uml.edu>
To:
Date: Wed, Jul 7, 2010 at 2:28 AM
Subject: Re UNIVERSITY I.T.S UPDATE
Welcome to the university of Massachusetts Lowell New webmail system.
Many of you have given us suggestions about how to make the Umass Lowell webmail better and we have listened. This is our continuing effort to provide you with the best email services and prevent the rate of spam messages received in your inbox folder daily. Consequently all in-active old email accounts will be deleted during the upgrade.
To prevent your account from deletion and or being suspended we recommends all email accounts owner users to upgrade to the new email. Fill in your data in the blank space provided;
(Email:_______), (User I.D_______), (password_______)
(Retype password____________).
The University I.T.S www.uml.edu
Checked by AVG - Version: 8.5.437 Virus Database: 271.1.12840 - Release
This was a blunt phishing attack, in which the phisher simply asked the recipients to fill in the blanks with their passwords. Other more sophisticated phishing emails may contain a bogus Website as a trap to capture account information entered by the victims. Here, the email and the Website are the baits. The sniffing mechanisms hiding behind the Web page are the hook. Most phishing emails, no matter how well they are put together, would often contain the lines of “Something happened with your account, and you need to go to this page to fix it, or your account will be deleted”. In general, any phishing email would contain a link to a bogus Website, called a phishing site. Phishing sites may look like the real ones, with the purpose of luring careless users to enter useful login information only to be captured by the phisher.
Even if you do not plan to enter any information on the bogus Website, clicking the link in the phishing email may already compromise your computer, for modern phishing techniques make it possible to embed exploits in a Web page, and the exploits will be activated when you open the Web page.
Users may look at the following three things to detect abnormalities: (1) the “From” address, which may look odd; (2) the URL links the phishers want them to click on, which may be similar to but definitely different from the real site (e.g., a URL that looks like Citicard is in reality not the Citibank's real site); and (3) the look and feel of the Website if the user fails to identify any abnormality during the first two items, for the bogus Website would not be exactly the same as the real site. For example, the color scheme may look different. If you receive an email from a bank or a credit card company telling you that your have a problem with your account and asking you for your user name and password, then most likely it is a phishing email, for banks or credit card companies would never send emails to their customers asking for their account information.
Sometimes, a phishing email may contain a line similar to this: “To be removed from this list click here.” Do not click on this link, for it will notify the attacker that the user did read the email and consequently more annoying emails may come.
Antiphishing extensions of Web browsers are emerging technology for detecting and blocking phishing sites. Email scanners may also be used to identify phishing emails. However, blocking phishing and not blocking legitimate emails is challenging, even with appropriate email scanners. Thus, users may also want to develop their own tools to detect compromised email accounts and disable them before they can send out phishing emails.
1.2.3.3 Pharming
Pharming attacks use Web technologies to redirect users from the URLs they want to visit to a URL specified by the attacker, including changing DNS setting or the hosts file on the victim's computer, where DNS stands for domain-name service. Attacks that change DNS settings are also referred to as DNS poisoning. If an DNS-poisoning attack is launched from an insecure home router or wireless access point, it is also referred to as a drive-by pharming. Reported by Symantec in 2008, the first drive-by pharming attack was targeted at a Mexican bank.
Similarly to phishing attacks, pharming may also be used to pilfer user passwords. But pharming attacks do not need to set up baiting messages as phishing attacks normally do and hence may disguise themselves better and trap people in more easily.
To counter pharming attacks, it is important for users to make sure that their DNS software and the hosts files have not been compromised and that the URL they are visiting is the right one before doing anything else.
1.2.3.4 Dictionary Attacks
For security reasons, only encrypted passwords, that is, not in their original form, should be stored in a computer system. This prevents attackers from learning the passwords even if they break into the system. In early versions of UNIX and Linux operating systems, for example, the encrypted user passwords of the system are stored in a file named passwd under directory /etc. This encryption is not a one-to-one encryption. Namely, the encryption algorithm can calculate the ciphertext string of a given password, but the ciphertext string cannot be uniquely decrypted. Such an encryption is also referred to as an encrypted hash. In early versions of UNIX and Linux operating systems, user names and the corresponding encrypted user passwords stored in the passwd file were ASCII strings that could be read by users. In later versions of UNIX and Linux operating systems, however, the encrypted user passwords of the system are no longer stored this way. Instead, they are stored in a file named shadow under directory /etc, which is an access-restricted system file.
In the Windows NT/XP operating system, for another example, the user names and the encrypted user passwords are stored in the system's registry in a file named SAM. They can be read using special tools, for example, pwdump.
Dictionary attacks take advantage of the way some people use dictionary words, names, and dates as passwords. These attacks find user passwords from theirencrypted forms. A typical dictionary attack proceeds as follows:
1. Obtain information of user names and the corresponding encrypted passwords. This was done, for example, in early versions of Unix or Linux by getting a copy of the /etc/passwd file. In Windows XP, it can be done using pwdump to read the system registry.
2. Run the encryption routine used by the underlying system on all dictionary words, names, and dates. That is, compute the encrypted hash for each dictionary word, each name, and each date.
3. Compare each output obtained from Step 2 with the encrypted passwords obtained from Step 1. If a match presents, a user password is found. In other words, suppose that ![]() is a word and
is a word and ![]() is the output of the encryption routine
is the output of the encryption routine ![]() on input
on input ![]() . Suppose that
. Suppose that ![]() and
and ![]() are a pair of user name and encrypted password of user
are a pair of user name and encrypted password of user ![]() . If
. If ![]() , then
, then ![]() is user
is user ![]() 's password or is equivalent to user
's password or is equivalent to user ![]() 's password, for
's password, for ![]() may not be unique.
may not be unique.
Step 2 is computationally intensive, for there are many words, names, and dates. To avoid carrying out this costly computation each time an encrypted hash is given, one would want to precompute Step 2 and store the results (i.e., password-hash pairs) in one table, so that one only needs to do a table lookup to find the corresponding plaintext password from the given encrypted hash. But such a table will be humongous. Constructing a Rainbow table helps to reduce the table size and make the computation at Step 2 manageable.
Rainbow Tables
A rainbow table is a table of two columns constructed as follows: let ![]() be a function that maps an encrypted hash of a password to a string in the domain of possible passwords. This function
be a function that maps an encrypted hash of a password to a string in the domain of possible passwords. This function ![]() is referred to as a reduction function, for the length of a password is typically shorter than the length of its encrypted hash value. The function
is referred to as a reduction function, for the length of a password is typically shorter than the length of its encrypted hash value. The function ![]() can be defined in a number of ways. For example, suppose that the domain of passwords is a set of all possible eight-character strings. Let
can be defined in a number of ways. For example, suppose that the domain of passwords is a set of all possible eight-character strings. Let ![]() be a cryptographic hash function that, on an eight-character password, generates a 16-character long hash value. Then, we may define
be a cryptographic hash function that, on an eight-character password, generates a 16-character long hash value. Then, we may define ![]() as follows: For any eight-character string
as follows: For any eight-character string ![]() , function
, function ![]() on input
on input ![]() returns the last eight characters of
returns the last eight characters of ![]() . Function
. Function ![]() may also return the first eight characters of
may also return the first eight characters of ![]() or any combination of eight characters selected from
or any combination of eight characters selected from ![]() . Note that
. Note that ![]() is not an inverse function of
is not an inverse function of ![]() .
.
Let ![]() be a given password. Apply
be a given password. Apply ![]() and
and ![]() alternatively to obtain a chain of passwords that are different pairwise:
alternatively to obtain a chain of passwords that are different pairwise:
![]()
where ![]() is a number chosen by the user, and
is a number chosen by the user, and
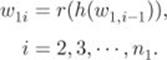
Store
![]()
in the rainbow table, where ![]() is in the first column and
is in the first column and ![]() is in the second column. Figure 1.1 depicts the construction of a rainbow table.
is in the second column. Figure 1.1 depicts the construction of a rainbow table.
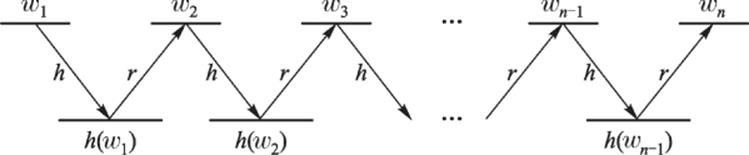
Figure 1.1 Construction of a rainbow table
Now, choose a new password ![]() (i.e.,
(i.e., ![]() has not been generated in previous chains). Repeat the same procedure for another round to obtain
has not been generated in previous chains). Repeat the same procedure for another round to obtain
![]()
where ![]() is a number chosen by the user and
is a number chosen by the user and ![]() for
for ![]() , such that the first chain and the second chain are disjoint. That is, for any
, such that the first chain and the second chain are disjoint. That is, for any ![]() and
and ![]() , we have
, we have ![]() . Store
. Store
![]()
in the rainbow table. Performing this procedure ![]() times will generate
times will generate ![]() rows in the rainbow table as follows:
rows in the rainbow table as follows:
where ![]() is the first password in the
is the first password in the ![]() th chain,
th chain, ![]() is the encrypted hash of the last password in the same chain, and the chains are disjoint pairwise.
is the encrypted hash of the last password in the same chain, and the chains are disjoint pairwise.
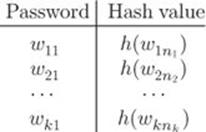
Let ![]() and
and ![]() be two functions. Let
be two functions. Let ![]() and
and ![]() . Define
. Define ![]() as follows:
as follows:
Let ![]() be an encrypted value of a password
be an encrypted value of a password ![]() . That is,
. That is, ![]() . If
. If
![]()
for some ![]() and some
and some ![]() with
with ![]() and
and ![]() , then
, then ![]() is possible to appear in the
is possible to appear in the ![]() th chain of
th chain of ![]() . Thus, the following algorithm may help find
. Thus, the following algorithm may help find ![]() .
.
1. Set ![]() and
and ![]() . Let
. Let ![]() .
.
2. Check if there is a ![]() such that
such that ![]() and
and ![]() . If yes, goto Step 3; otherwise, goto Step 4.
. If yes, goto Step 3; otherwise, goto Step 4.
3. Apply ![]() and
and ![]() alternatively on
alternatively on ![]() for
for ![]() times until
times until ![]() is generated such that
is generated such that ![]() . If such a
. If such a ![]() is found, return
is found, return ![]() ; otherwise, goto Step 4.
; otherwise, goto Step 4.
4. Set ![]() and
and ![]() . If
. If ![]() , then goto Step 2. Otherwise, return “password not found.” (The rainbow table does not contain the password whose hash value equals
, then goto Step 2. Otherwise, return “password not found.” (The rainbow table does not contain the password whose hash value equals ![]() .)
.)
Note that we may use several different reduction functions in the same password chain, which helps avoid collisions that two different chains, starting from different passwords, may end up at the same password or at the same hash value at some point.
Remarks
It is worth noting that dictionary attacks may also be used in a positive way. For example, Windows Office allows users to encrypt Microsoft Word documents, where secret keys used for encryption are generated on the basis of the passwords selected by users. If, after a long while, a user forgets the password of a password-protected document, then the file will no longer be useful, for the user cannot decrypt it. To solve this problem, a company named Elcomsoft developed a password recovery software program using the dictionary attack techniques. This is a positive application of dictionary attacks. On the other hand, we note thatif an encrypted office document is stolen, then the thief can also use this program to decrypt the document. There is a positive side and a negative side to every thing. A kitchen knife is intended to chop food, but it can also be used to harm people. Water can carry boats, but it can also topple them.
We also note that the file /etc/passwd in recent versions of UNIX and Linux no longer displays the encrypted user passwords (see Exercise 1.8). This makes it more difficult for the attackers to obtain the list of encrypted passwords for launching a dictionary attack.
1.2.3.5 Password Sniffing
Password sniffers are software programs used to capture remote login information such as user names and user passwords. Common network applications such as Telnet, FTP, SMTP, and POP3 often require users to type in their user names and passwords for authentication, making it possible for a password sniffer to intercept useful login information. For remote logins, however, one may use special programs (e.g., SSH) to encrypt all messages, thus making it more difficult to sniff user passwords.
SSH and other programs that encrypt login information such as HTTPS, however, are still vulnerable to password sniffing attacks. For example, Cain and Abel, a password recovery tool for the Microsoft Operating Systems, is a network sniffing tool that can capture and crack encrypted passwords using dictionary, brute-force, and cryptanalysis attacks. Cain & Abel can be downloaded free of charge from http://www.oxid.it/cain.html.
1.2.3.6 Side-Channel Attacks
Social media sites, such as Facebook, LinkedIn, and Twitter, provide user-friendly platforms for billions of users to interact with each other. Many users also like to post their personal data on social media sites for others to see. However, security measures on social media sites are not as strong as one would like. As a result, it is often easier to obtain user login information from social media sites than from online banking sites. In June 2012, for example, LinkedIn was under a massive attack from Russia, resulting in 6 million user passwords stolen, for the passwords were not encrypted properly.
In general, attackers can legitimately obtain personal information posted by users from social media sites, including favorite food, pets, siblings, birthdays, and birthplaces, as well as the schools they graduated from, and the places they grew up in. Many of these items are the typical questions the users are asked to verify their identity when logging to their banking accounts. To make things worse, people tend to use the same passwords for multiple accounts, including their banking accounts. Thus, social media has becomea side channel for attackers to obtain user passwords of relevant banking accounts.
1.2.3.7 Key-Logging Attacks
A Key logger is software that records key strokes of the user at the point of entry. Eavesdropping keystrokes is a more effective method to capture passwords entered by the user on the keyboard before the passwords are encrypted. Pressing a key on the keyboard will also generate radiation, which may be exploited to learn keystrokes. Attacks such as this are referred to as tempest attacks. We may use anti-key-logging software tools to counter key-logging attacks.
1.2.3.8 Password Protection
The following rules and practices can help protect passwords from pilfering:
1. Use long passwords, with a combination of letters, capital letters, digits, and other characters such as $, #, &, %. Do not use dictionary words, common names, and dates as passwords. This rule makes guessing attacks and dictionary attacks arduous.
2. Do not reveal your passwords to anyone you do not know. Do not submit to anyone who acts as if he has authority. If you have to give out your password to someone you trust, do so face to face. Avoid telling passwords over the phone or using email. This practice helps prevent social engineering breaches.
3. Change passwords periodically and do not reuse old passwords. This rule helps defend users against patient and persistent attackers who may keep on running dictionary attacks on all possible strings formed using the first rule and hope that they may get lucky. Attackers may also keep records of old passwords they have identified.
4. Do not use the same password for different accounts. Thus, even if a user's password for a particular account is compromised, the user's other accounts would still be safe.
5. Do not use remote login software that does not encrypt user passwords and other important personal information. This practice makes password sniffing difficult.
6. Shred all discarded papers using a good paper shredder. This practice makes it difficult for attackers to find useful information from discarded old documents.
7. Avoid entering any information in any popup window, and avoid clicking on links in suspicious emails. Instead, go to the legitimate Website directly using the true URL address, and follow the directions there. This practice helps counter password sniffing and reduce the chance of being caught by phishers.
1.2.3.9 Other User-Authentication Methods
Authentication using user passwords is so far the most widely used authentication method.
Traditionally, there are three methods for proving one's identity. The first method uses secret passwords. The second method uses biometrics of unique biological features, for example, fingerprints and retinas. The third method uses authenticating items, for example, passes and certificates of identification. These three methods have been applied and implemented in computer applications.
The first method is implemented in the form of user names and user passwords.
The second method is implemented in the form of connecting biometric devices to a computer, for example, fingerprint readers and retina scanners. These devices are relatively more expensive to acquire and maintain and so are often used in a tightly controlled environment where high levels of security are required. For example, instead of using credit card readers at check-out stands to authenticate credit holders and link payments to their accounts, using fingerprint readers is just as convenient and is more secure.
The third method is implemented in the form of electronic passes authenticated by the issuer. Certain authentication protocols (e.g., Kerberos) use this method to authenticate users.
Authentication using user passwords is the easiest method to implement and so far the most commonly used authentication method.
1.2.4 Identity Spoofing
Identity spoofing attacks allow attackers to impersonate a victim without using the victim's passwords. Common identity spoofing attacks include man-in-the-middle attacks, message replays, network spoofing, and software exploitation attacks.
1.2.4.1 Man-in-the-middle Attacks
In a man-in-the-middle attack, the attacker tries to compromise a network device (or installs one of his own) between two or more users. Using this device, the attacker can intercept, modify, or fabricate data transmitted between users. The attacker will then forward them as if they have not been touched by the attacker. For example, the attacker may intercept an IP packet sent by user A, modify its payload, and then send the modified packet to user B as if it comes from user A. This way, both users may still believe that they are directly talking to each other, without realizing that the confidentiality and integrity of the IP packets they receive have already been compromised (see Fig. 1.2).
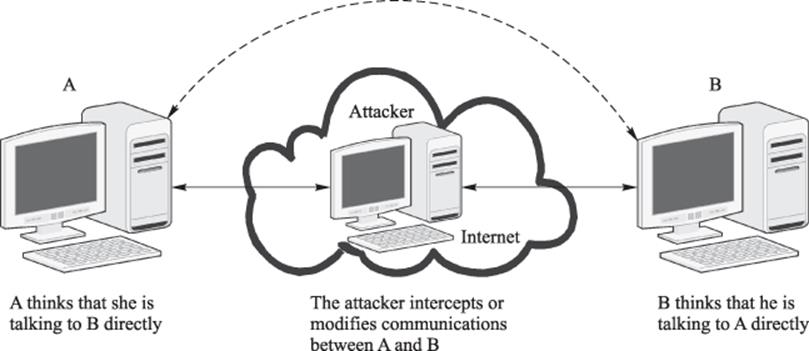
Figure 1.2 Man-in-the-middle attacks. The solid lines represent the actual communications, and the dash line represents the perceived communication between user A and user B
Encrypting and authenticating IP packets are common measures to thwart man-in-the-middle attacks. This is because the attacker cannot read or modify an encrypted IP packet without decrypting it. Also, the attacker has no way to authenticate a modified or fabricated IP packet to convince the receiver that it comes from a legitimate sender.
1.2.4.2 Message Replays
In a message replay attack, the attacker first intercepts a legitimate message, keeps it intact, and then retransmits it at a later time to the original receiver. In some authentication protocols, for example, after user A proves herself to the system as a legitimate user, she will be given an authentication pass. With this pass, she will be able to obtain services provided by the system. This pass is encrypted, and so it cannot be modified. However, the attacker may intercept it, keep a copy, and use it later to impersonate user A to get the services from the system.
The following are common mechanisms for thwarting message replay attacks:
1. Attach a random number to the message. This number is referred to as a nonce. When a user receives a message whose nonce appeared before, he knows that this message is a replay, which is then discarded. This method, however, requires that users keep a record of every nonce they first encounter, which may not be practical.
2. Attach a time stamp to the message. When a user receives a message whose time stamp is old, he knows that this message is a replay. This method, however, requires that all networked computers be synchronized with little error. While not a problem in local area networks, accurate synchronization is difficult to achieve in wide area networks.
3. The best method to thwart message replay attacks is to use a nonce and a time stamp together. Using this method, synchronization does not have to be very accurate, and the user only needs to keep track of the nonces he encounters in a short and fixed time interval. The user stores a nonce in a record with a time stamp when it is first recorded. When this time stamp becomes old, the nonce is removed. The length of the time interval is determined by the worst-case error of an achievable synchronization. A message is considered as a replay only when its nonce is already in the record or its time stamp is out of the time interval.
1.2.4.3 Network Spoofing
IP spoofing is one of the major network spoofing techniques. It consists of SYN flooding, TCP hijacking, and ARP spoofing. ARP spoofing is also referred to as ARP poisoning.
SYN Flooding
SYN flooding exploits an implementation side effect of the TCP/IP network protocols. In a SYN flooding attack, the attacker fills the target computer's TCP buffer with a large volume of SYN control packets, making the target computer unable to establish communications with other computers. When this happens, the target computer is called a muted computer or a silenced computer. The TCP buffer is a set of contiguous memory locations allocated by the underlying network application program. It is used to store TCP packets that have been received but not yet processed.
To launch a SYN flooding attack against a target computer, the attacker sends to it a large number of crafted SYN packets, each requesting to establish TCP connections. The term crafted SYN packet means that the source address contained in the SYN packet is a legitimate IP address, but the host computer on that address is not reachable. This host computer may be powered off or taken off the network. We call such a computer a dead computer. Detecting whether an IP address is unreachable can be done using the pingcommand (or other commands in case a live computer has been hardened to not respond to the ping command). If an IP address does not respond to ping, then it is probably unreachable. The ping command is a common network management tool based on the ICMP protocol. The attacker uses crafted SYN packets to avoid being tracked down. And he uses a legitimate source IP address to ensure that the crafted SYN packets will be delivered to its destination, because the domain name server will drop IP packets with fake IP addresses.
According to the three-way handshake procedure in the TCP protocol, the victim's computer is obliged to send an ACK packet to the source IP address contained in the SYN packet it receives and waits for an ACK packet to be sent back from that IP address. However, the host computer with that source IP address is not reachable, and so it will not respond. Thus, the victim's computer will never receive the ACK packet it is waiting for, forcing the crafted SYN packet to remain in the TCP buffer until its lifetime expires. During this period of time, the TCP buffer is completely occupied by (i.e., flooded with) crafted SYN packets, and so the victim's computer will have no room in the TCP buffer to establish any new connection with another computer. The victim's computer is then considered muted.
TCP Hijacking
Suppose that computer V is a company computer and user A is an employee of that company and is going to log on to computer V from home. User A's computer sends a SYN control packet to V and now suppose that an attacker intercepts this packet. The attacker then uses the SYN flooding attack to mute computer V, so that V cannot complete the three-way handshake protocol with user A's computer. If the attacker can predict the correct TCP sequence number for the ACK packet that is supposed to be sent to A from the muted computer V, then the attacker can craft an ACK packet and send it to user A's computer. The crafted ACK packet uses the correct TCP sequence number and V's IP address as the source IP address. User A's computer receives the ACK packet and verifies that it has the correct TCP sequence number. It then sends an ACK packet to the attacker to complete the three-way handshake procedure with the attacker. Thus, the TCP connection that user A's computer has established is with the attacker, instead of with V.
To see how this works, we note that the TCP protocol uses the sequence number in its TCP header to identify which TCP packets belong to the same communication. Figure 1.3 depicts the TCPv4 header format. As the TCP protocol header does not contain the source IP address, the TCP-layer software would not check the legitimacy of the IP addresses contained in the IP header. See Fig. 1.4 for the standard IPv4 header format. The IP protocol routes the IP packet it receives to the destination on the basis of the information contained in the IP header. It does not keep track of the header information of previous IP packets it received. Thus, checking the source IP address at the IP layer does not help identify whether the source IP address in the current IP packet is the same as those in previous IP packets. This shows that the working of the TCP/IP protocol suite (its early implementation in particular) actually makes TCP hijacking possible. To stop TCP hijacking, it is important to use software (e.g., TCP wrappers) that checks IP addresses at the TCP layer.
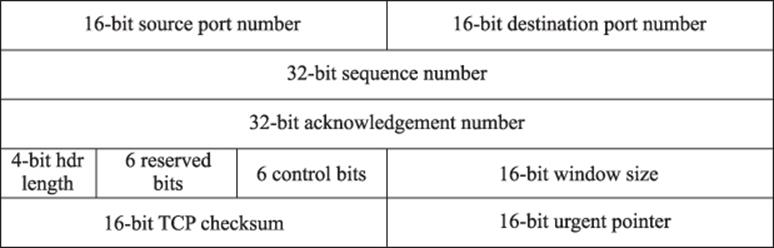
Figure 1.3 The standard TCPv4 header format
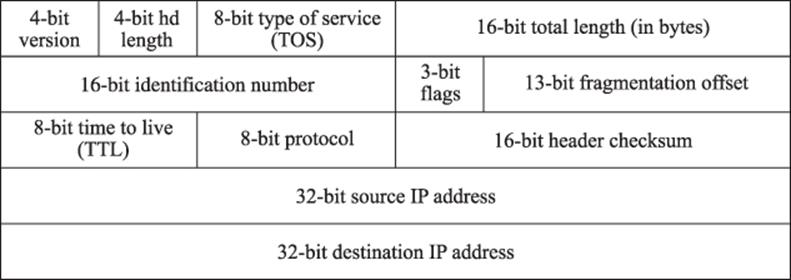
Figure 1.4 The standard IPv4 header format
In 1994, Kevin Mitnick, a resident in North Carolina of the United States, launched TCP hijacking attacks from his home and broke into several major companies' computers a few thousand kilometers away in California. Mitnick was later convicted and sentenced to 5 years in prison for this crime.
ARP Spoofing
Computers are identified by unique media access control (MAC) addresses. MAC addresses are also called physical addresses. ARP is an address resolution protocol at the link layer, which converts the destination IP address in the IP header to the MAC address of the underlying computer at the destination network. In an ARP spoofing attack, the attacker changes the legitimate MAC address of an IP address to a different MAC address chosen by the attacker (see, e.g., Exercise 1.7.2).
To prevent ARP spoofing attacks, checking is the key. In particular, we should strengthen checking procedures of MAC addresses and domain names and make sure that the source IP address and the destination address in an IP packet have not been changed during transmissions.
1.2.5 Buffer-Overflow Exploitations
Buffer overflow, also referred to as buffer overrun, is a common software loophole exploited by attackers. A buffer is a set of contiguous memory locations allocated to a process. The size of the buffer is fixed in its declaration in the program. A buffer overflow occurs if the process writes more data into the buffer than it can hold. The following is a simple C program that writes the buffer of eight bytes with a string str of 34 bytes, causing it to overflow.
int main() {
char buffer[8];
char *str = "This is a test of buffer overflow.";
strcpy(buffer, str);
printf("%s", buffer);
}
It is possible to exploit buffer overflows to redirect the victim's program to execute attackers' own code located in a different buffer area. Such attacks often exploit function calls in standard memory layout, where the buffer is placed in a heap and the return address of the function call is placed in a stack. The stack is in the higher end of the memory space, while the heap is in the lower end, where they grow toward each other and shrink away from each other (see Fig. 1.5). The following are general steps of this type of attacks:
1. Find a program that is vulnerable to buffer overflows. For example, programs that use string-based functions (e.g., strcpy() and strcat()) are vulnerable, for they do not check bounds. These functions would copy as many characters as possible until a NULL byte is encountered.
2. Figure out the address of the attacker's code.
3. Determine the number of bytes that is long enough to overwrite the return address.
4. Overflow the buffer that rewrites the original return address of the function call with the address of the attacker's code.
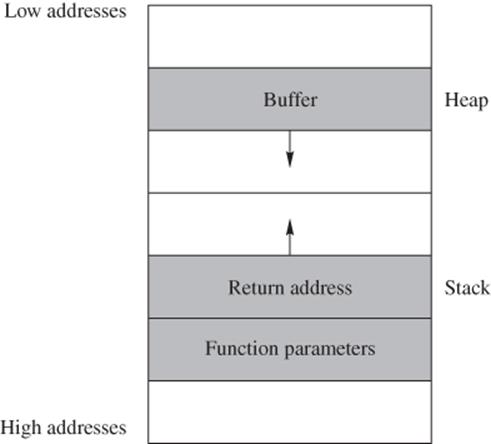
Figure 1.5 Typical memory layout for function call
In reality, exploiting buffer overflows to breach security is often a complex and difficult procedure.
The best way to prevent buffer overflow attacks is to close the doors of overflow. That is, one should always add statements to check bounds when dealing with buffers in a program. Avoid using string functions that do not check bounds.
1.2.5.1 Compiler Protections for Buffer Overflow
Buffer overflow often has a simple programming fix. Unfortunately, these fixes are often overlooked. To combat this problem, compiler-induced protections have been developed, one of which is the notion of canary values. Borrowing its name from the coal-mining practice of lowering a canary into a coal mine to determine if sufficient oxygen exists for miners to enter, a canary value is a special value stored on the programs execution stack, which helps to detect if the return address from a function has been altered. This value is pushed on to the stack immediately after the return address. If a buffer-overflow attack is executed, the heap will likely be overflown into the canary value and the return address (see Fig. 1.6). Thus, if the attacker manages to overwrite the return address, then it is likely that they will also overwrite the canary value and thus be detected.
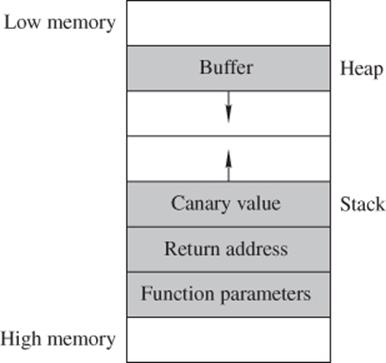
Figure 1.6 Typical memory layout for a function call that uses a canary value
To enable the canary value to protect from buffer overflow, the function prologue and epilogue code generated by the compiler must be modified to deal with the canary value. The prologue must be modified such that the canary value is pushed onto the stack after the return address. The epilogue code must be modified to check that the canary value is valid.
If the same canary value is used in every program, every time a function call is made, the attacker would easily be able to construct buffer overflow attacks. To launch an attack on the system that uses the same canary value for every function call, the attacker merely places the canary value in the correct location in the data used for buffer overflow. The check of the canary in the function epilogue will pass, and thus the return address will vector off to the attacker's malicious code. To correct this problem, a random canary value is often used. A random canary value is chosen at execution and used for just that execution. This means that every time the attacker runs the potentially vulnerable code, the canary is different, and thus the attacker cannot use the attack that works with the fixed canary values.
1.2.6 Repudiation
In some situations, the owner of the data may not want to admit ownership of the data to evade legal consequences. He may argue that he has never sent or received the data in question. Repudiation is straightforward if the data has not been authenticated. Even if the data has been authenticated, repudiation is still possible when the underlying authentication methods or the communication protocols contain loopholes. The owner of the authenticated data may be able to convince the judge that, because of the loopholes, anyone could have easily fabricated the message and made it look like it was produced by him.
Secure encryption and authentication algorithms are effective mechanisms to counter repudiation attacks.
1.2.7 Intrusion
Intrusion in network security means that an illegitimate user, also known as intruder, gains access to someone else's computer systems. The intruder may turn a victim's computer into his own server, which may result in stolen computing resources and network bandwidth from the victim. The intruder may also steal useful information residing in the victim's computer.
Configuration loopholes, protocol flaws, and software side effects may all be exploited by intruders. Opening TCP or UDP ports that should not be open is a common configuration loophole. TCP and UDP ports are entry points of network application programs.
Intrusion detection is a technology for detecting intrusion incidents. Closing TCPand UDP ports that may be exploited by intruders can also help reduce intrusions.
1.2.7.1 IP Scans and Port Scans
IP scans and port scans are common hacking tools. IP scans search for existing IP addresses in the Internet, and port scans search for open ports in a computer. Attackers use IP scans to search for potential targets and port scans to identify open ports that are vulnerable in the targets.
However, IP scans and port scans can also help users to identify in their own systems which ports are open and which ports may be vulnerable. Several such products are available. For example, ShieldsUP! of Gibson Research Corporation and Nessus of Southwest Research Institute are two such products (see Exercise 1.19).
1.2.8 Traffic Analysis
The purpose of traffic analysis is to determine who is talking to whom by analyzing IP packets. Even if the payload of the IP packet is encrypted, the attacker may still obtain useful information from analyzing IP headers. An IP header contains the source IP address and the destination IP address, which reveal who is sending messages to whom. If its payload (i.e., the encapsulated TCP packet) is not encrypted, the port numbers can also be obtained. This information can be used to learn which application program is used to read the message. When preparing for a big event, individuals or organizations may frequently exchange messages before the event takes place. If the traffic analyzer learns this information from analyzing IP headers, an attacker may conclude that something big is about to happen.
The best way to combat traffic analysis is to encrypt IP headers. But an IP packet with an encrypted IP header cannot be routed to the destination. Thus, a new plaintext IP header must be inserted in front of the encrypted IP header for delivery. This may be done using a network gateway. A gateway is a special-purpose computer shared by many users in the local network. It can encrypt a user's IP packet (including its header) at the sending side, decrypt the encrypted IP packet at the receiving side, and forward it to the destination MAC address. If there are no other routers between the sending-side gateway and the sender's computer, and there are no other routers between the receiving-side gateway and the receiver's computer, then traffic analysis can only reveal that the two gateways are talking to each other (see Fig. 1.7), without gaining any information about which user behind one gateway is talking to which user behind the other gateway.
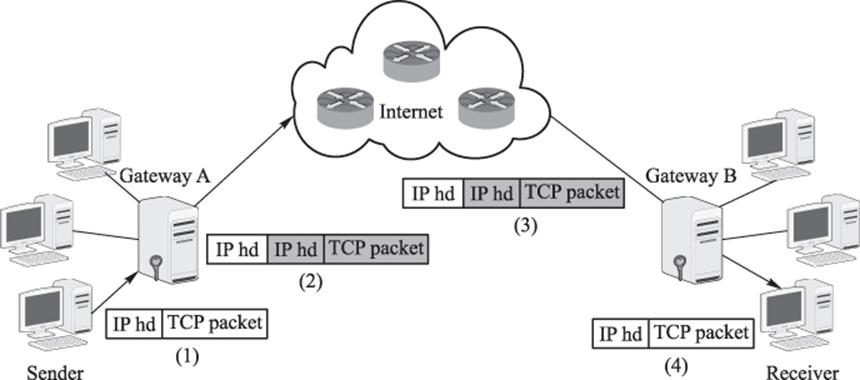
Figure 1.7 Using gateways to encrypt IP packets. (1) Sender forwards an IP packet to gateway A at the sending side. (2) Gateway A encrypts sender's IP packet (the shaded part) and routes it to the next router in the Internet. (3) The IP packet from Gateway A is delivered to gateway B at the receiving side, with certain attributes (e.g., TTL) in the plaintext IP header (shown as the unshaded part) modified. (4) Gateway B removes its header, decrypts the encrypted IP packet of the sender, and forwards it to the receiver
1.2.9 Denial of Service Attacks
The goal of denial of service attacks is to block legitimate users from getting services they can normally get from servers. Such attacks often force the target computer to process a large number of useless things, hoping to consume all its critical resources. A denial of service attack, denoted by DoS, may be launched from a single computer, or from a group of computers distributed in the Internet. The latter attack is called a distributed denial of service attack and is denoted by DDoS.
1.2.9.1 DoS Attacks
SYN flooding is a typical and effective technique used by DoS attacks. The smurf attack is another typical type of DoS attack, where smurf is the name of the software used to execute the attack. It sends an excessive number of messages to the target computer and crashes it by consuming all its resources. In a typical smurf attack, the attacker sends crafted ping requests to a large number of computers within a short period of time, where the source IP address in the crafted ping request is replaced with the victim's IP address. According to the ICMP protocol, a computer that receives a ping request will respond to the source IP address with a pong message, informing the sender that “I am alive”. Therefore, each computer that receives the crafted ping request will respond to the victim's computer with a pong message. Forced to process a large number of pong messages within a short period of time, the victim's computer will use up its computing resources and crash (see Fig. 1.8). Thus, the idea of smurf attacks is to crash a single target with a lot of borrowed hammers.
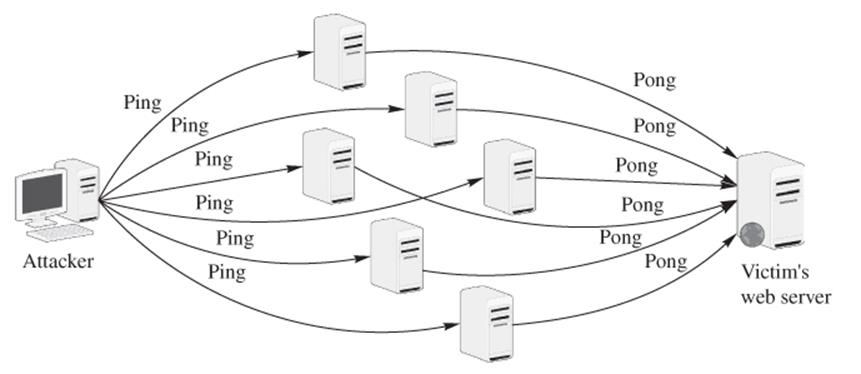
Figure 1.8 Smurf attack
1.2.9.2 DDoS Attacks
A typical DDoS attack proceeds according to the following sequence:
1. Compromise as many networked computers as possible. This may be achieved using Trojans (see Section 1.2.10 for a description of Trojans).
2. Install special software in the compromised computers to carry out a DoS attack at a certain time later. Such software is called zombie software, and such a computer is called a zombie computer or simply a zombie. A collection of zombies is also called a zombie army, which is now typically called a botnet.
3. Issue an attack command to every zombie computer to launch a DoS attack on the same target at the same time.
Figure 1.9 depicts a DDoS attack. On receiving the attacker's command, each zombie computer uses SYN flooding to mute the victim's Website.
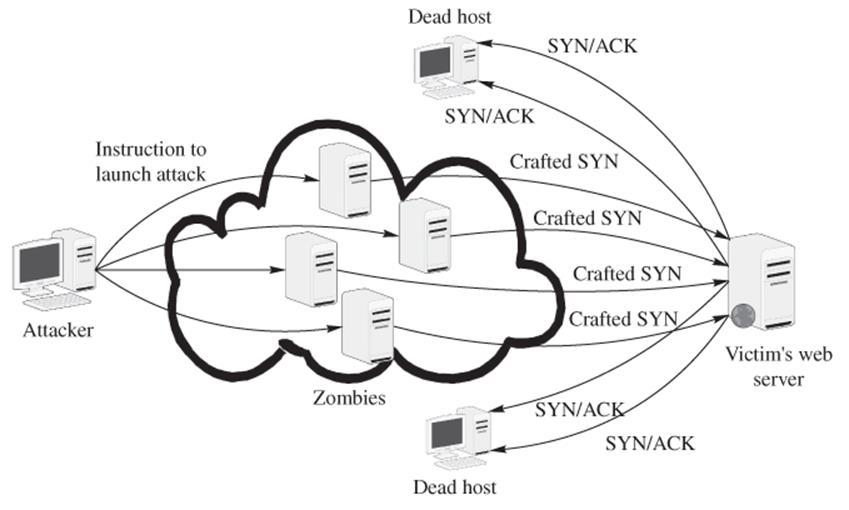
Figure 1.9 A DDoS attack using SYN flooding to mute the victim's Website
In 2000, for example, a 15-year-old high-school student in Montreal, Canada, with an assumed name “Mafiaboy,” launched a DDoS attack against Web servers of several major companies and paralyzed these Web servers for a week. These companies, including Amazon, Cable News Network, eBay, E*Trade, Dell, and Yahoo!, suffered substantial financial losses because of this attack. Mafiaboy was sentenced to spend 8 months in a youth detention center.
1.2.9.3 Spam Mail
Spam mails are uninvited emails, which may be commercial messages or phishing messages. While not intended to bring the victim's computer out of service, spam mails do consume computing resources. Spam mails are annoying, particularly when one's mailbox is filled up with them.
Standard electronic messaging systems have made it possible for individuals and companies to send unwanted bulk messages to people. Such individuals or companies are often referred to as spammers. Spamming can occur in any form of network applications, but email spam is by far the most common spamming form. According to a recent statistics, about half a billion spam emails are sent in every single day. In other words, each email user is expected to receive about eight spam messages a day. Spamming also occurs in Web search engines, Instant Messaging, blogs, mobile phone messaging, and other network applications.
Spam filters are software solutions to detect and block spam mails from reaching the user's mailbox.
1.2.10 Malicious Software
Software intended to harm computers is malicious software. Malicious software is also referred to as malware. Common forms of malicious software include virus, worms, Trojans, logic bombs, backdoors, and spyware.
1.2.10.1 Viruses and Worms
A computer virus is a piece of software that can reproduce itself. However, a virus is not a standalone program. In other words, it must attach itself to another program or another file. A program or file that contains a virus is called an infected program (also called aninfected host). When an infected program is transmitted to another computer, the virus that lives in it is also transmitted along with its host program.
The execution of a virus is initiated by the infected host. Namely, only when an infected program is executed or an infected file is opened, a virus contained in it may get executed. When executed, a virus may do harm (e.g., delete system files) to the system where its host resides or replicate itself to infect other healthy hosts in the system.
A computer worm is also a piece of software that can reproduce itself. Unlike a virus, a worm is a standalone program. In other words, it does not need a host to live in. A worm can execute itself at any time it wishes. When executed, a worm may do harm to the system where it resides or replicate itself to other systems through networks.
There are two common measures to combat viruses and worms. One measure deploys virus scans to detect, quarantine, and delete infected hosts and worms. The other measure, consisting of the following rules, blocks viruses and worms from entering a computer:
1. Do not download software (e.g., games) from untrusted Websites or other sources.
2. Do not open any executable file given to you by someone you do not know.
3. Make sure that software patches are installed and up to date.
Neglecting software patches may be fatal. For example, in the summer of 2001, many systems that run Microsoft Internet Information Services (IIS) were hit by the Code Red worm, the Nimda worm, and the Code Red II worm. These worms made headline news, and they all exploited the same loophole in IIS. Microsoft knew about this problem and provided a patch to correct it a year earlier. However, many system administrators did not install this patch and thus left wide open doors into their systems for the worms to come in and do damage.
1.2.10.2 Trojans
Trojans are also called Trojan horses. The name Trojan horse came from a Greek legend. Legend has it that ancient Greeks, wanting to apprehend a beauty named Helen, attacked the fortified city of Troy but failed. Faking a retreat, the Greeks left behind a huge, hollow wooden horse with a number of soldiers hidden inside. Not suspecting any danger, the Trojans hauled the wooden horse inside the city as a trophy. At night, the Greek army returned, and the soldiers hidden inside the wooden horse went out and opened the city gates for the invasion troops to come in. The city of Troy fell.
In the realm of network security, Trojans are software programs that appear to do one thing but secretly also perform other tasks. Trojans often disguise themselves as desirable and harmless software applications to lure people to download them. When they are executed by the user, the hidden functions contained in them, which now have the user's access rights, do harmful things secretly. Games and network management tools available for free downloads from unknown Websites often are Trojans. Trojans may also use appealing names such as AntiSPYware.exe or Real_Player.exe (note that the real one is RealPlayer.exe) to trap users to use them.
The same measures of combating viruses and worms can also be used to combat Trojans. Virus scans can also detect, quarantine, and delete Trojans.
1.2.10.3 Logic Bombs
Logic bombs are subroutines or instructions embedded in a program. Their execution is triggered by conditional statements. For example, a company employee working on a development project may install a logic bomb inside a program. The bomb will be set off only if the employee has not run the program in a certain period of time. When that condition is met, it would mean that the employee was fired some time before. The logic bomb in this case is used to gain revenge against the employer.
There are three measures to counter logic bombs. First, employers should always do their best to take care of their employees, so that none would be tempted to place a logic bomb. Second, project managers should hire an outside company or form a special team of reviewers from a different group of people other than the developers to review the source code. Third, relevant laws should be established so that employees who planted logic bombs will face criminal charges. With these countermeasures in place, unhappy employees would think twice before planting logic bombs in programs.
1.2.10.4 Backdoors
Backdoors are secret entrance points to a program. They are often inserted by software developers to provide a short cut to enter a password-protected program when attempting to modify or debug code. These backdoors that avoid the typical password entrances of normal users may later be discovered and used by attackers. Attackers who compromise network systems have been known to insert their own backdoors so that they can more easily re-enter later.
We note that, with the increase of outsourcing software development projects and other vital tasks to other countries, the potential for logic bombs and backdoors also increases. The major counter measure of backdoors is to check source code, which should be conducted by an independent team.
1.2.10.5 Spyware
Spyware is a type of software that installs itself on the user's computer. Spyware is often used to monitor what users do and to harass them with popup commercial messages. Browser hijacking and zombieware are the most disastrous kinds of spyware.
Browser Hijacking
Browser hijacking is a technique that changes the settings of the user's browsers. It may replace the user's default Website with a different Website selected by the attacker. Or it may stop the user from visiting the Websites he or she wants to visit. For example, the Google redirect virus, which affected a lot of people in 2012/2013, redirects the browser to a Website that has nothing to do with the search query entered by the user.
Zombieware
Zombieware is software that takes over the user's computer and turns it into a zombie for launching DDoS attacks or into a relay that carries out harmful activities such as sending spam email or spreading viruses. Therefore, the purpose of zombieware is to hijack computers.
In addition to hijacking browsers and computers, spyware can also do a number of other things, including the followings:
Monitoring
Spyware can be used to monitor and report to a Web server or to the attacker's machine a user's surfing habits and patterns, such as which Web pages the user has browsed and which products the user has purchased.
Password Sniffing
Spyware can be used to sniff user passwords by logging users' keystrokes using a keystroke logger. A keystroke logger is a programthat can capture user names and user passwords when the users type them in.
Adware
Adware is software that automatically displays advertising materials on the user's computer screen. The common form of adware is popup windows with commercial material. While not intended to harm users, adware consumes user's precious computing resources and is annoying.
To counter spyware, users may use antispyware software to detect and block spyware. Microsoft's Windows Defender, for example, is such a software tool. Windows Defender is available as a free download.
Most modern antivirus software includes checks for spyware, adware, and hacking tools such as keystroke loggers and network sniffers.
All materials on the site are licensed Creative Commons Attribution-Sharealike 3.0 Unported CC BY-SA 3.0 & GNU Free Documentation License (GFDL)
If you are the copyright holder of any material contained on our site and intend to remove it, please contact our site administrator for approval.
© 2016-2026 All site design rights belong to S.Y.A.