Computer Forensics with FTK (2014)
Chapter 7. Working with PRTK
This chapter will cover the Password Recovery Toolkit (PRTK) and Distributed Network Attack (DNA). Both are used to provide a password-cracking function. You can use PRTK and DNA in computer forensic investigations to access password-protected files or system passwords.
The main difference between these tools is that PRTK runs on a single machine only and DNA uses multiple machines across the network.
You will understand this difference and how to use the tools for the password recovery of a large number of popular software applications.
An overview of PRTK
The use of encryption and data protection through the use of passwords has steadily grown among the users of computers. Encryption is seen as a strategic business issue and is adopted by most companies.
Given this scenario, PRTK becomes a fundamental tool to assist in the digital investigation process, supporting the attempt to access the protected data contained in the evidence.
You can download the latest stable version of PRTK and DNA at http://www.accessdata.com/support/product-downloads.
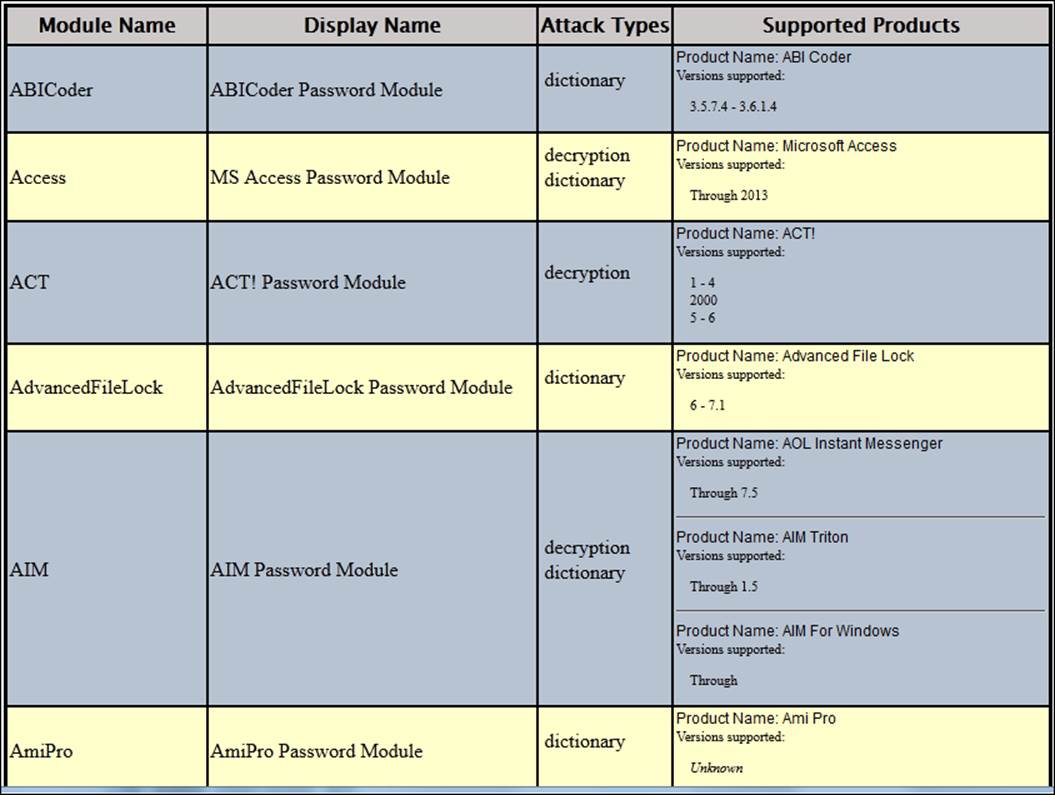
PRTK supports a wide variety of products for password cracking. To access the full list of supported products and types of attack, click on Help and then click on Recovery Modules.
The following figure shows a small example of the supported products:
Understanding the PRTK interface
The PRTK interface is very simple and has a few options. The process is basically automatic and does not require much user intervention. The main functions of the interface are as follows:
· Menu: Through this, you can access all the functionalities and options for configuration and tuning.
· Toolbar: This provides quick access to the main features of the tool.
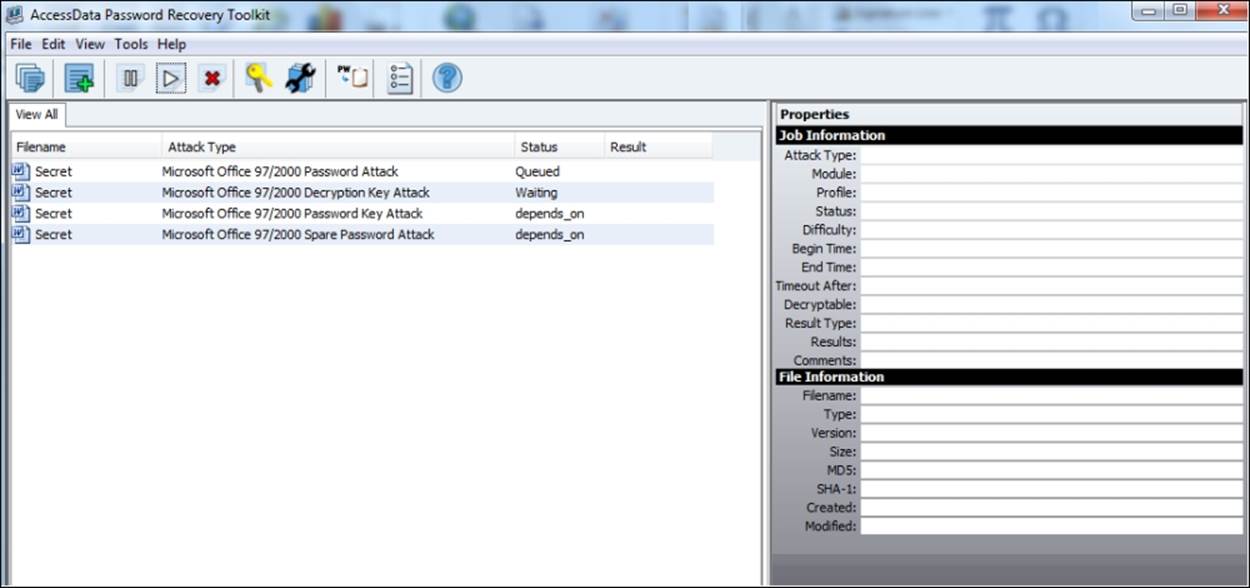
· View All: This is the main viewer. You can track the status of the password-cracking attack.
· Properties: This is where you can view information about a file in the attack process.
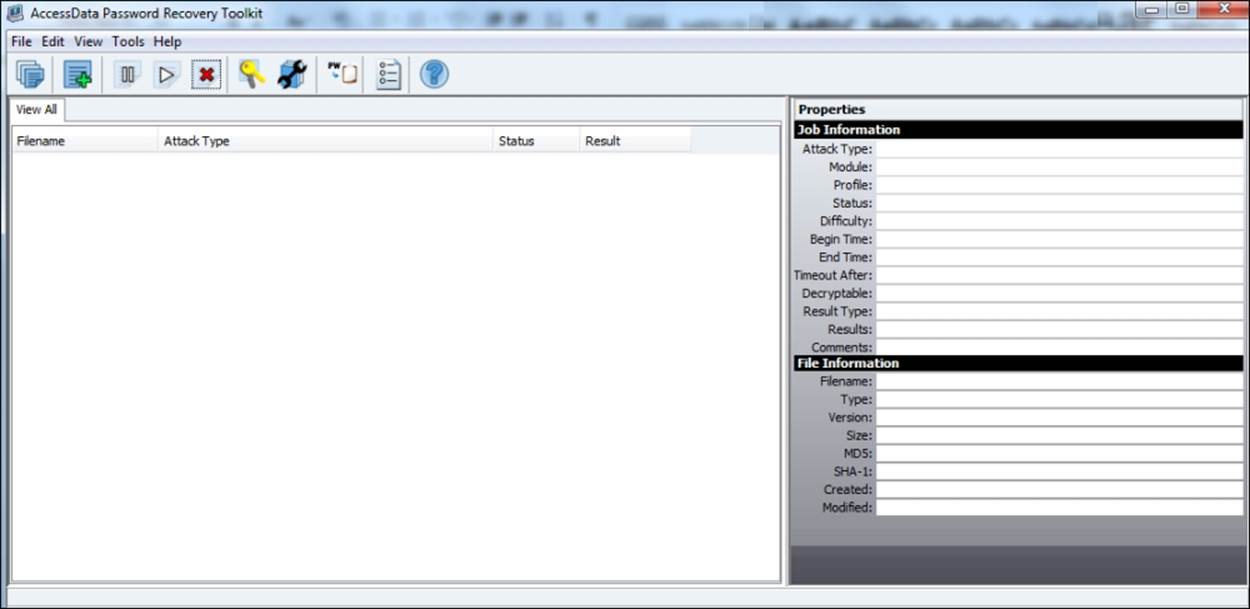
The main features and configurations will be discussed in the following topics.
Creating and managing dictionaries
Dictionaries are an optimization tool used for password recovery. By using dictionaries, specific candidate passwords are tested before the more general ones. This utility creates a variety of custom dictionaries for use with PRTK.
Tip
Create backups of the word lists and dictionaries because if the dictionary is modified or deleted, you cannot recover it again.
The dictionary utility can be used to create or modify several types of dictionaries.
To use the dictionary utility, perform the following steps:
1. Click on Tools and then click on Dictionary Tools.
2. The AccessData Dictionary Import Utility screen will appear. Click on Dictionary Tools again.
3. Select the specific tool that you need to use (listed in the following table).
The following table lists tools that can be accessed from the Dictionary Tools menu and their functions:
|
Tool |
Function |
|
Dictionary Browser |
To view the words in each dictionary or to delete a particular dictionary or dictionaries |
|
Dictionary Info |
To view specific details about a dictionary, such as the dictionary type, encoding, language, word count, and description |
|
Biographical Dictionary Generator |
Builds the dictionaries of candidate passwords from a collection of biographical details and from combinations of the biographical data entered |
|
Pass-phrase Dictionary Generator |
Builds dictionaries from a phrase file and using subphrases from the phrase file |
|
Permutation Dictionary Generator |
Builds dictionaries from a wordlist file and using the permutations of words from the wordlist file |
|
Standard Dictionary Generator |
Builds custom dictionaries using a wordlist file |
|
Golden Dictionary Merge |
Merges two golden dictionaries into a single golden dictionary |
Tip
The Biographical Dictionary is very useful for cracking passwords because it is very common for people to create their passwords based on the combinations of their personal information.
Starting a session for password recovery
The utilization of the password recovery tool is very simple. With a few clicks, your password cracking session is ready and running.
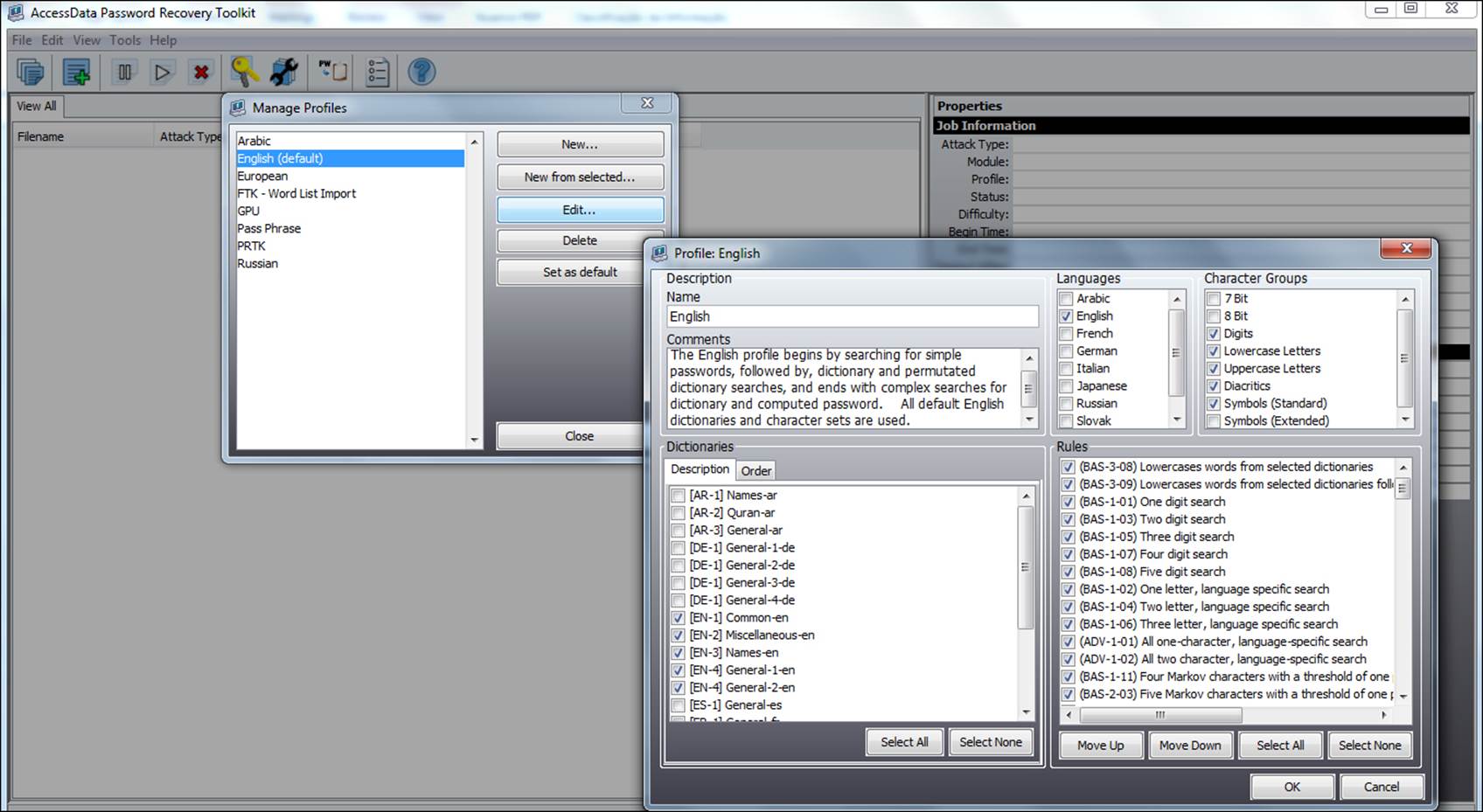
Managing profiles
To use PRTK for processing a password recovery, you need to select an appropriate profile for your case investigation. A profile is a set of specific rules that must be used to define which types of password recovery will be used.
You can use any of the default profiles or create your own.
Note
By convention, this book uses the default profile English.
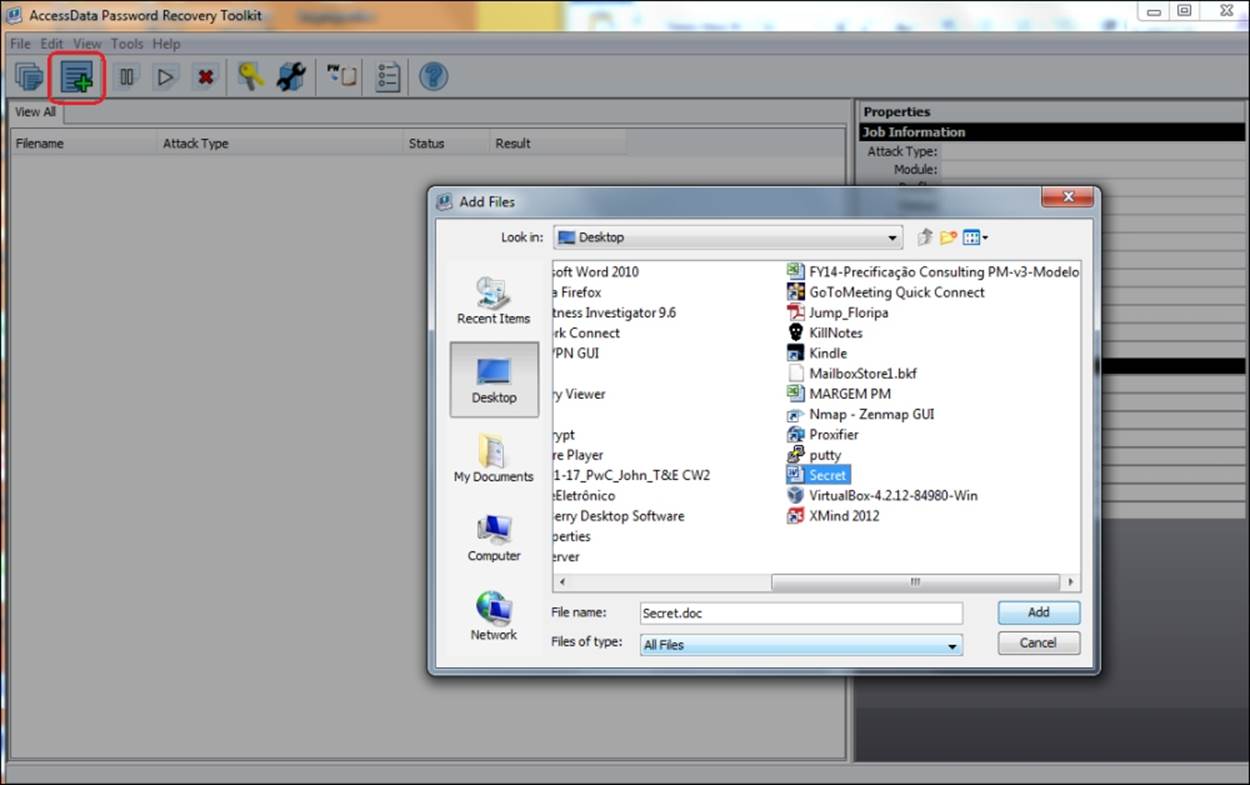
To start a new session of password cracking, perform the following steps:
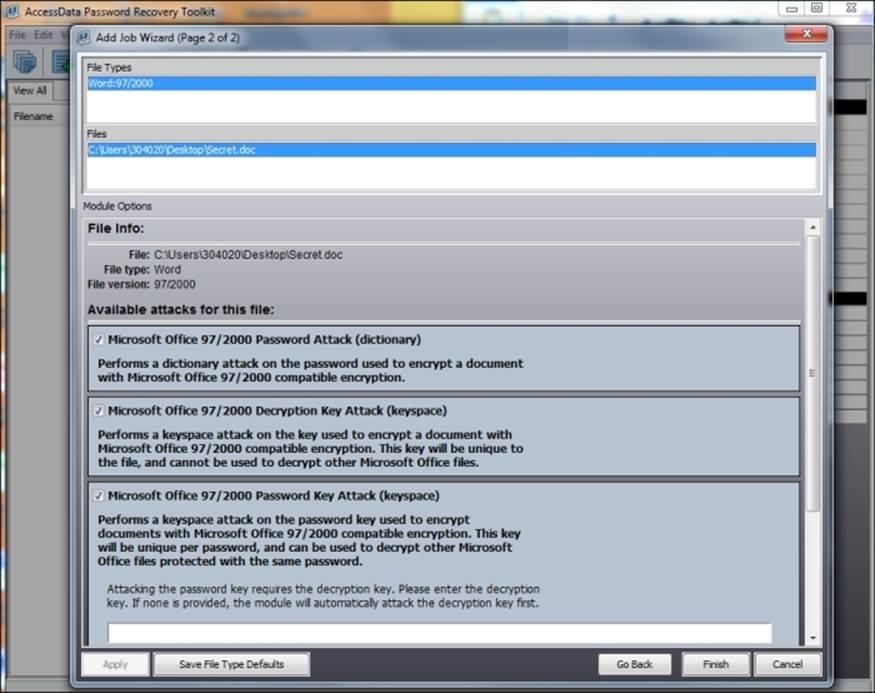
1. Go to File | Add Files or click on the corresponding button on the toolbar as shown in the following screenshot.
2. Select the protected file and click on Add.
3. The suggested types of attacks will appear. You can change the type if necessary or leave the default model presented.
4. Click on Finish to start the cracking process.
The cracking process will start, and you can follow the progress status of each of the techniques.
The time for obtaining the password can vary greatly depending on the complexity of the software application or the algorithm used for the password.
Additionally, the process for password cracking depends largely on the capability of the hardware, mainly the processor. There is specific equipment for the activity of cryptanalysis, which uses video cards (GPU) to gain speed.
Note that the process is fully automated, requiring few interactions or modifications.
Tip
You can use the drag-and-drop command to add files to PRTK.
DNA
As discussed earlier, the process of password cracking requires a lot of hardware resources.
DNA is a tool that can assist in this process since it uses sharing and distribution between the computers on the network resource.
DNA has an interface that is very similar to PRTK features with an exception of solution architecture.
There are two components to the DNA system as follows:
· Supervisor: This is a machine that controls the Worker machines in the DNA system and the jobs that they process. Install it before the Workers.
· Worker: This is responsible for processing jobs for decryption or password cracking. You should run the appropriate Worker installation program on each machine in the system.
Summary
This chapter covered the first steps to use the PRTK Forensics tool and a brief vision of the DNA solution.
Even though a simple solution of using their resources is extremely advanced, it can recover passwords from almost all commonly used files.
PRTK is a mandatory tool used in digital investigations since you will most likely find some protected files that may contain the key to the outcome of your investigation.
All materials on the site are licensed Creative Commons Attribution-Sharealike 3.0 Unported CC BY-SA 3.0 & GNU Free Documentation License (GFDL)
If you are the copyright holder of any material contained on our site and intend to remove it, please contact our site administrator for approval.
© 2016-2026 All site design rights belong to S.Y.A.