Beginners guide to hacking and penetration testing (2017)
Email Spoofing with Social Engineering Toolkit:
For this demo we will be using the Social Engineering Toolkit by TrustedSec https://www.trustedsec.com/social- engineer-toolkit/ This toolkit is something of a "One Stop Shop" for social engineering and Penetration testing. The program is free and runs on Linux and OS X. The program is also bundled into Backtrack and Kali Linux. Below is an example of a credential harvesting attack. We would use this to steal a person's login and password for a site.We will be doing this demo in Backtrack.

To launch: Click on Exploitation Tools-Social Engineering Tools"-Social Engineering Toolkit-Set
![]()
Next you want to select Option 1 Social-Engineering Attacks
![]()
Next select Website Attack Vectors
![]()
Next we will select Credential Harvester Attack Method
![]()
Site Cloner allows us to copy a website or use a custom template
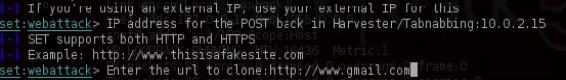
When we clone a site will be required to enter in the attacker computer (Our) IP address. You can find this by typing ifconfig for Linux and OS X machines without the quotes. Under the next field type in the website to clone. Besure to add in the full address.

Once we have the program running we need to get the address out. For this we can do this by QR code, text, etc. In this case we will email it out. In this case I will be sending out the email though Gmail. I will embed the link by clicking the Insert link option.
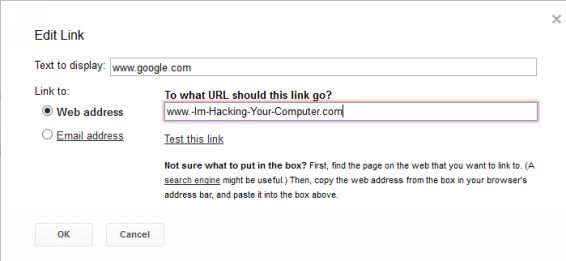
Next fill in the address of where you want the victim think's they are going to. In our case we will make sure the Text to display says http://www/gmail.com Under the "Web address" we will make it our attacker IP address.

Once we have the link embedded, it will appear to be a legitimate address.
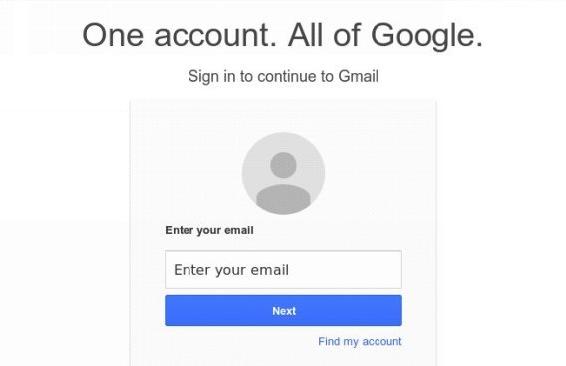
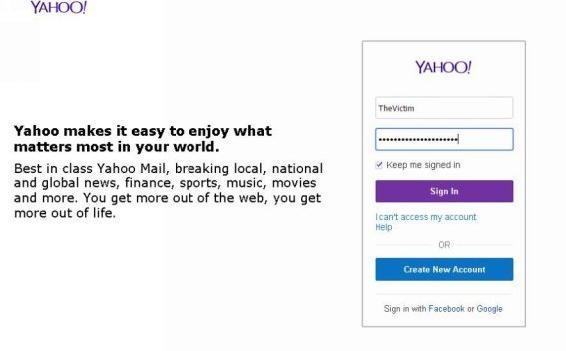
When the victim clicks the link it will appear legitimate. We simply wait for them to login.
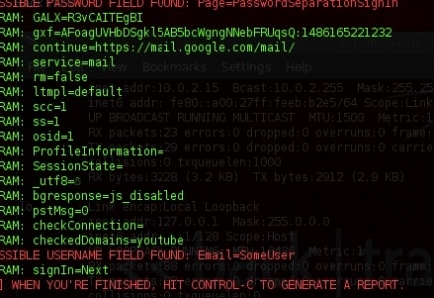
Once the victim logs in their user name and password will be displayed for us.
Tip(s):
• When crafting the email be sure to check your spelling!
• Make the reasoning enticing for them to login
• You will need to spoof the sender, be sure to craft your email to match that particular sender. Speech, signatures, images, etc.
Z-Shadow http://z-shadow.co/index.php
Another method is Z-SHADOW. This is a website based program. Personally I don't trust it so I entered in a fake email.

Once you create an account you will see several different templates in various languages. Click on the language you want for the template that you want to use and send it to your victim.
Once we send the link to the victim and they enter in their credentials it'll be sent to our Z-Shadow
account.

On our Z-Shadow account (You may need to click the refresh) under My Victims we will see a list of
websites, username, password, date, time, and the IP address of all of our victims. It's important to note that these passwords only stay for 15 days!
Note:
When phishing or vishing a target for penetration testing it's important to keep in mind that even though we are acting like an attacker, we still need to follow certain rules. Now while it may not be out of the scope of work per say to use certain bait tactics to have a person click or open an email link (An example might be if you know your target's child is sick in the hospital, sending an email out posing as the hospital with a critical life threating informationthat needs to be addressed by clicking a link). While the example given may not be out of the scope of work it may be crossing certain lines that will result in that user being angry. As penetration testers we should not cross certainlines for ethical reasons.
All materials on the site are licensed Creative Commons Attribution-Sharealike 3.0 Unported CC BY-SA 3.0 & GNU Free Documentation License (GFDL)
If you are the copyright holder of any material contained on our site and intend to remove it, please contact our site administrator for approval.
© 2016-2026 All site design rights belong to S.Y.A.