HOW TO HACK: HACKING SECRETS EXPOSED: A BEGINNER'S GUIDE (2014)
Chapter 10. Hiding Information
Once the hackers gain access and take control of the system, the next step they may try to do is to hide some critical files and information on it. The hacker may decide to hide files for later execution or use the victim's compromised system to store information secretly so that it can be accessed later and sent to the final destination where it is intended to go. In this chapter we will discuss some of the popular techniques to hide files and information on a system. Let us start with the simple ones and gradually advance to more complex techniques.
WINDOWS HIDDEN ATTRIBUTE
Using the Windows built-in hidden attribute is by far the simple and easiest way to hide files and folders on a system. To enable hidden attribute just follow the instructions as given below:
1. Right-click on the file or folder that you intend to hide and select "Properties" from the pop-up menu.
2. In the "Properties" window, under the "Attributes" section check the box which says "Hidden" and click on "OK".
This will make the selected file or folder go invisible. To view the hidden files and folders follow the instruction below:
1. Open the "Control Panel" by clicking the "Start" button
2. Now click on "Appearance and Personalization" and then on "Folder Options".
3. Switch to "View" tab, check the option "Show hidden files, folders and drives" under "Advanced Settings" and click on "OK".
This should unhide all the hidden files and folders. However, the drawback of this method is that most users are aware of this and hence the hidden files can easily be uncovered. In order to counter this drawback, some of the advanced information hiding methods are discussed below.
NTFS ALTERNATE DATA STREAMS
Alternate Data Stream (ADS) is a Windows hidden stream supported on NTFS file system used to store metadata of a file such as attributes, word count, access and modification time etc. Whenever a file is created on NTFS file system, Windows automatically creates an ADS for it. Even in directory listing only the actual file is visible but its ADS is kept hidden.
It is even possible to add additional ADS to an existing file to store hidden information in it. Hackers often use this technique to store malicious codes in compromised systems without the knowledge of the victims.
Suppose if you want to hide information inside an image or any other file, just follow the steps mentioned below:
1. Open the Windows command prompt.
2. Type the following command and hit Enter.
Command Syntax: notepad file-name:ADS-name
Example Command: notepad flowers.jpg:hiddeninfo
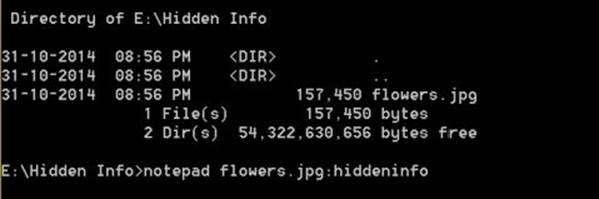
Figure 10. 1
As shown in the above snapshot, I am issuing the above command on flowers.jpg present inside the folder named Hidden Info.
3. Now Windows will create a new ADS for the specified file and open it in a new notepad with a message window "Do you want to create a new file?" as shown below.
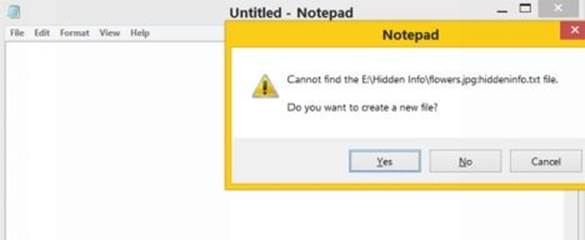
Figure 10. 2
4. Click on "Yes", and type the content that you wish to hide on to it and once you are done save and close the notepad.
5. Now, all your secret message will be stored in a new ADS called hiddeninfo inside the file flowers.jpg.
To the outside world, the flowers.jpg is just an image file but only the hacker know that it contains hidden data inside it. Even if the file is moved to another system (NTFS only), it still carries the hidden information along with it.
To view the hidden info all you need to do is again type the same command as notepad flowers.jpg:hiddeninfo in the command prompt. This will open up the ADS contained inside the flowers.jpg file in a notepad displaying all the hidden text that was previously stored.
ADS technique has a small drawback! If this file is copied or moved on to a different file system such as FAT32, all the ADS information will be dropped and the hidden information will be lost.
STEGANOGRAPHY
Steganography is a means of obscuring data where secret messages are hidden inside computer files such as images, sound files, videos and even executable files, so that no one except the creator will know about the existence of stealth information in it.
Steganography may also involve the usage of cryptography where the message is first encrypted before it is concealed in another file. Generally, the messages appear to be something else such as an image, sound or video so that the presence of secret data in it remains unsuspected.
The main advantage of steganography over other information hiding methods is that, it will not arose suspicion even if the files fall in the hands of a third party. Unlike cryptography which only encrypts information, stegnography uses both encryption and obscurity of data in a normal file. This makes stegnanography hard to detect as the files look completely normal from outside.
Stegnographic tools implement intelligent algorithms to carefully embed the encrypted text messages or binary data inside other larger files such as an image, audio, video or an executable file. Some tools will embed the encrypted data at the end of another file so that there will be enough room for storing larger data.
There are many steganograpic tools available online but only a few are able to work flawlessly. I did not find any tool that worked perfectly on both small and large data. To counter this problem, I have managed to develop my own tool that can work perfectly on all types of files and all size of data. I have named the tool as StegoMagic. You can download it from the following link.
Download StegoMagic
The zip file contains two versions of StegoMagic: One for encrypting the text messages and the other for encrypting binary files. StegoMagic_TXT can be used to hide text messages in other files such as an image or a sound file. StegoMagic_BIN can be used to hide one binary file in another such as an executable file inside an image or an image inside a video file and so on.
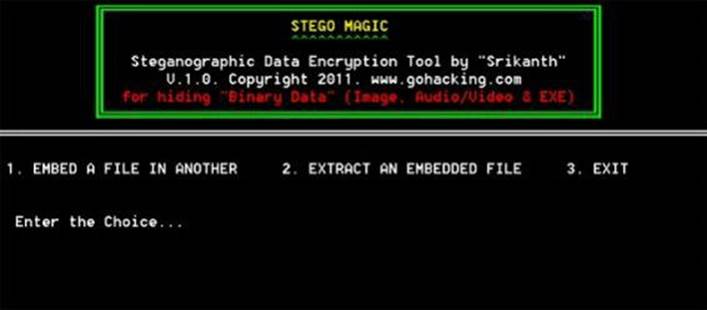
Figure 10. 3
With StegoMagic, there is no limitation on the size and type of the file that you are intending to hide. For example, you can hide a video of size 1 GB in an image of size 1 MB or hide an executable file inside a WORD document. The tool is pretty straightforward to use and requires no special understanding of the concept.
At the end of the encryption process, a secret decryption key will be generated and the same is required during the decryption process.
How to Use StegoMagic?
Suppose you want to hide a text message inside a .JPG image file:
1. Place the .JPG image file and the text file (.txt) in the same folder as that of StegoMagic_TXT.exe
2. Run StegoMagic_TXT.exe (with administrator rights) and follow the screen instructions to embed the text message inside the JPG image.
3. Note down the secret decryption key.
4. Now you can send this image to your friend via email. To decrypt the hidden message, your friend should load this JPG file onto the StegoMagic tool and use the secret decryption key.
USING TOOLS FOR HIDING INFORMATION
You can also use several open-source tools and programs to hide important files and folders on a given system. Here is a list of are some of the handy tools that you can use:
1. Free Hide Folder
This is a freeware tool for Windows that can hide any number of folders and make them go completely invisible for others. You also have the option to password protect the program for additional safety.
2. Wise Folder Hider
Wise Folder Hider is a freeware used to hide your personal folder(s) or file(s) to somewhere else in your PC or in removable devices, in which way you can protect your privacy with passwords by following easy steps.
3. WinMend Folder Hidden
WinMend Folder Hidden is a free file/folder hiding tool. While ensuring the absolute system safety, this application can quickly hide files and folders on local partitions and/or on removable devices. The hidden files/folders will be safely hidden whether the drive is accessed in another operating system on the same computer or reinstalled on another computer. You can set a password for this application. Hidden data can be displayed and unhidden only when the user enters the valid password.