HOW TO HACK: HACKING SECRETS EXPOSED: A BEGINNER'S GUIDE (2014)
Chapter 3. Introduction to Linux
Linux is a UNIX-like operating system which is open-source and freely available for download. Compared to Windows operating system Linux is more secure, stable, reliable, multi-user capable and compatible with both server and desktop usage. This makes it one of the most popular operating system next to Windows.
WHY LINUX?
As an ethical hacker, it is most essential to have a sound understanding of the Linux platform, its usage and commands. Linux is widely recognized as the "hacker's operating system" and if you are wondering why, the reasons are below:
· Since it is a freeware, highly secure and stable operating system, millions of servers on the Internet runs on Linux.
· Unlike Windows OS which is built on graphical user interface (GUI), Linux is built on command user interface (CUI) and thus offers greater control and customization options for hackers.
· Some of the best hacking scripts and programs are designed only for Linux.
WINDOWS VS. LINUX
It is no doubt that Windows is the most popular desktop operating system known for its user friendliness and graphical user interface. As a result, most computer users across the world are familiar with the Windows operating system but are new to Linux. If you are fairly new to Linux and are wondering what's the difference between Windows and Linux, here is a quick comparison between the two:
Comparison between Windows and Linux
|
Windows |
Linux |
|
Known for its user friendliness and ease of use. |
Known for its security, stability, flexibility and portability. |
|
Widely used for desktop usage by home and office users. |
Widely used for server usage by enterprise and corporations. |
|
The operating system is mainly based on graphical user interface (GUI). |
The operating system is mainly based on command user interface (CUI). |
|
Designed to operate with only one user at a time. |
Designed to support simultaneous multi-user operation. |
|
More than 70,000 viruses are reported for Windows till date. |
Only around 80-100 viruses are reported for Linux till date and hence more secure. |
|
Since it is based on GUI it is easy for users to learn and operate. |
Since it is based on CUI it is somewhat difficult for users to learn and operate. |
|
Comes as commercial product and hence available only on purchase. |
Comes as an open-source and hence freely available. |
|
Examples of Windows based OS include Windows 2000, XP,Vista, 7 and 8. |
Examples of Linux based OS include Ubuntu, Fedora, Red Hat, Debian, CentOS etc. |
Table 3. 1
CHOOSING A LINUX DISTRIBUTION
A Linux distribution is a collection of software and applications compiled around the Linux kernel (central component of the operating system). You can choose from a wide variety of Linux distributions like Ubuntu, Fedora or Debian where each of them contain their own collection of software and applications but shares a common Linux kernel. As a beginner you can choose Ubuntu as it easy to install and user friendly. You can find the download link and installation guide from the official Ubuntu website for which the link is mentioned below:
Official Ubuntu Website: http://www.ubuntu.com/
RUNNING LINUX FROM A LIVE DISK
There are two ways to use a Linux operating system. One is to install the operating system on to the hard drive just like you do it for the Windows. However, this method requires a prior experience of installing and configuring the operating systems. If you are new to Linux or do not have a prior experience of OS installation, you can use a live disk option such as CD or DVD to run and use Linux. This in fact is a good alternative to installation and provides an easy way to get Linux running on your system without modifying any of its previous settings and existing file system. But this option does not save your work upon shutting down your computer and hence suitable only for usage like penetration testing and learning.
One of my favourite distribution for hacking and penetration testing is Kali Linux. This is based on Debian GNU/Linux platform and comes in the form of a live DVD with an option to install as well. You can download the ISO image for the DVD version freely from the Kali Linux official website. The link to the website is given below:
Kali Website: https://www.kali.org/downloads/
After the download is complete you can burn the ISO image onto the DVD using a free program like ImgBurn. This should give you a bootable live Kali DVD. For your reference, I have used the 64-bit 1.0.9a version of the Kali Linux live DVD in all my examples and demonstrations throughout this book.
LINUX BASICS
Linux operating system was developed in 1991 by Linus Torvalds when he was a student of Helsinki University, Finland. He posted about the source code that he developed in the Minix news group. The feedback was good and the source code started to spread around the world via FTP and over the years Linux became a very popular operating system. Today, many great network programs, security tools and servers including DNS, Email and Web server are being developed for Linux by programmers and hackers around the world.
Linux System Organization
The functioning of Linux is organized in terms of the following layers as shown in the Figure below:
· Hardware Layer consists of the actual hardware devices like CPU, Memory, Hard Disk Drive etc.
· Kernel is the core component which lies at the heart of the operating system that directly interacts with the hardware using the machine language.
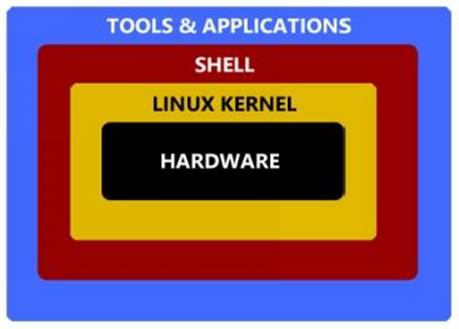
Figure 3. 1
· Shell (or the command interpreter) acts as a mediator that takes commands from the user and then conveys them to the kernel which ultimately executes them.
· Tools and Applications reside on the outer crust and gives user most of the functionalities of an operating system.
Linux Directory Structure
A directory structure is the way in which the file system and its files of an operating system are displayed to the user. People who are new to the Linux operating system and the structure of its File System often find it troublesome and messed up in dealing with the files and their location. So, let us begin to explore some of the basic information about the Linux File System.
Any standard Linux distribution has the following directory structure as shown below:
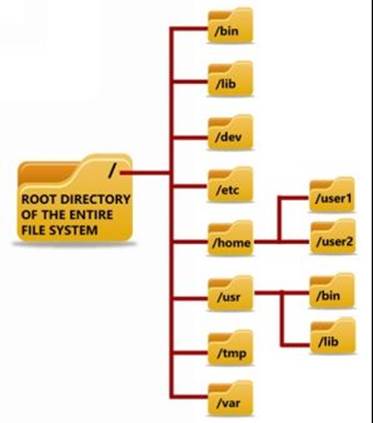
Figure 3. 2
Below is a brief description of the purpose and contents of each directory:
/ - ROOT Directory
Every single file and the directory of the Linux file system starts from the root directory. Only "root" user has the write privilege to this directory.
/bin - Binaries
Contains executable binary files required for booting and repairing of the system. Also contains file and commands required to run in single user-mode such as: ls, ping, grep etc.
/lib - System Libraries
Contains system libraries and kernel modules required for the booting of the system.
/dev - Device Files
Contains device related files for all the hardware devices of the system.
/etc - Configuration Files
Contains configuration files required by all programs. It also contains start-up and shutdown shell scripts used to start or stop individual programs.
/home - Home Directories
This forms the "home directory" of individual users to store their personal information. Every time a new user is added, a new directory is created in the name of the user under "/home".
/user - User Programs
This directory is used to store executable binaries, documentation, source-code files and libraries for second level programs.
/tmp - Temporary Files
Contains temporary files for system and users.
/var - Variable Files
Contains files whose size is expected to grow. Examples of such files include log files, print queues, lock files and temp files.
Linux Commands
All commands in Linux are typed in lowercase and are case sensitive. Each Linux command has to be typed and executed in a window called "terminal emulator" or simply referred to as a terminal. It is a program similar to the command prompt of Microsoft Windows where a user can run the commands and get the results displayed. A terminal simply takes the user commands, passes it on to the shell for execution and displays the results back to the user.
To run commands in the terminal, you will have to first load the Linux from the Live DVD that you have created. To do this, just insert the Kali Linux DVD into the drive, boot from it and select the "Live option". Once the booting is completed you should see your desktop loaded on your screen.
To start the terminal window, just click right-click on the desktop and select the option Open in Terminal as shown in the below snapshot 3.1:
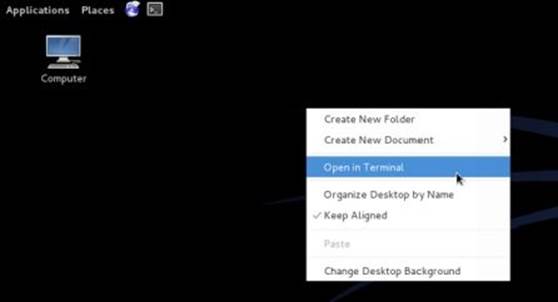
Figure 3. 3
Once the terminal window is loaded you should be able to start typing the commands. A snapshot of the terminal window is shown below:
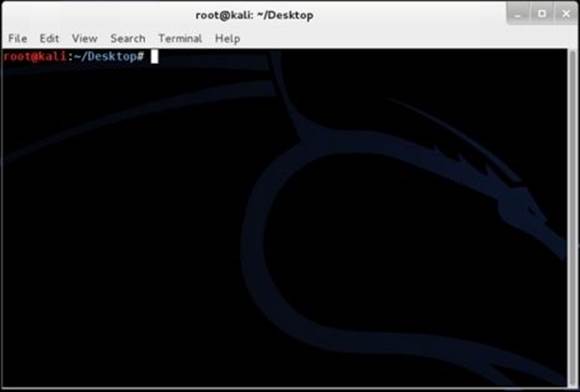
Figure 3. 4
Creating Files
There are two commands for creating files: touch and cat. Here is how they are to be used:
# touch sample
This creates an empty file called "sample". If you want to create multiple empty files quickly it can be done as follows:
# touch sample1 sample2 sample3 sample4 sample5
In order to store a few lines of data onto the file just type the following command:
# cat > sample
When you press the Enter key, you will find the cursor positioned in the next line waiting for you to type the content that you want to store in the file "sample". Just type in the following line:
This is a sample file containing some sample text.
Once you are done, press Ctrl+D. This will save the contents onto the file and automatically take you back to the # prompt. Now, to display the contents of the file "sample" just type the command as follows:
# cat sample
This should display the contents of the file as shown in the snapshot below:
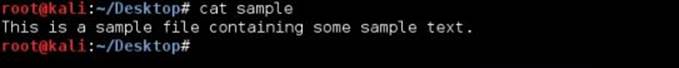
Figure 3. 5
Editing Files
To edit a given file one has to use the vi command. In order to edit a given file "sample" the command is as follows:
# vi sample
When you type the above command and hit Enter, you should see the contents of the file "sample" displayed in the vi editor window as shown in the Figure 3.6:
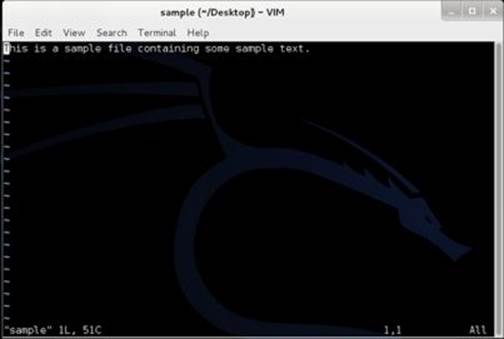
Figure 3. 6
In order to start your edit process you need to enter the INSERT mode by pressing the key i. Now, your cursor should move freely inside the editor window allowing you to make necessary changes to the content. Once you are done with the editing, press the Esc key. Now type :wq as shown in the below snapshot and hit Enter. The w stands for write/save and q stands for quit. This should save changes to your file, close the vi editor and take you back to the # prompt. If you are to quit without saving changes just type :q! instead of :wq and hit Enter.
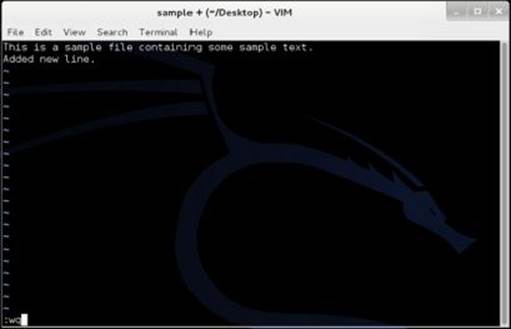
Figure 3. 7
Listing Files and Directories
To display the list of files and directories the command used is ls. ls is the Linux equivalent of DIR command in Windows. To list the files and directories just type the following command and hit Enter.
# ls
Deleting Files and Directories
In Linux rm command is used to delete files and directories. To delete a file use the command as shown below:
# rm samplefile
When you hit Enter, you are asked for delete confirmation. Just type y and hit Enter again. This should complete the deletion of the file "samplefile".
To delete a directory and all its contents use the following command:
# rm -r sampledir
When you hit Enter, you are asked for a delete confirmation. Just type y and hit Enter again. This should complete the deletion of the directory "sampledir" and all the contents inside it.
Logging Out
Once you are done with your work, you can close the terminal window using the exit command as follows:
# exit
Connecting to a Remote Host
So far we have discussed ways to execute commands on your own Linux computer. However, since Linux is a multi-user operating system it is possible for the users to connect to a computer running Linux even if they are miles away from its physical location. In this section we will discuss some of the ways through which you can connect to a remote computer and execute commands on it.
SSH (Secure Shell) is the most popular and the easiest way to accomplish this task. This is a protocol that allows a client to connect to a remote host and carry out operations on it.
SSH on Linux
If you are on a Linux computer, connecting to another Linux computer is very easy. Just open the Terminal window and type the following command:
Command Syntax:ssh username@host
Here username means username of your account on the remote computer and host can be a domain name such as xyz.com or the IP address of the remote computer. The following examples make it more clear:
# ssh john@xyz.com
# ssh john@66.226.71.129
# ssh root@xyz.com
# ssh root@66.226.71.129
If the user exists on the target machine, the connection will be established and you will be asked to enter the password. Once you enter the password and hit Enter (password entered will be invisible due to security reasons), you will be granted access to the target Linux machine where you are free to execute any command on it as discussed in the previous section.
SSH on Windows
You can connect to a remote Linux machine even if you are using a Windows computer. This can be done using a small freeware program called PuTTY which is an SSH client and a terminal emulator for Windows. You can download it from the link below:
Download PuTTY: http://www.chiark.greenend.org.uk/~sgtatham/putty/download.html
After the download, double-click on the application putty.exe, enter the hostname or IP address of the target machine, select the SSH option and click on the button "Open" as shown in the below snapshot:
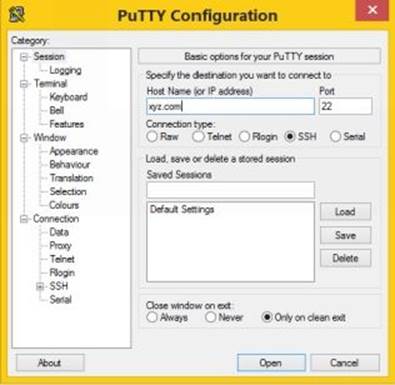
Figure 3. 8
This should establish the connection with the remote Linux machine and ask you to enter the Login as (username) followed by the password (will be invisible due to security reasons). Once you have entered the correct login details you will be able to execute commands on the target machine.
FURTHER REFERENCES
This chapter has dealt with some of the basic concepts and command examples of Linux operating system so as to lay the groundwork for your further learning. In order to emerge as a professional hacker, it is necessary to have a sound understanding on Linux and master its commands. For this reason, I have a few recommendations for your further references.
Here is a list of some of the useful websites to expand your Linux knowledge:
· Linux Official Website
· Free Linux Training
· Linux Knowledge Base
· Linux Visual Training
Here is a list of some of the great books worth reading:
· How Linux Works
· A Practical Guide to Linux Commands, Editors, and Shell Programming