CCNP Security SISAS 300-208 Official Cert Guide (2015)
Introduction
Welcome to the world of Cisco Career Certifications and the CCNP-Security. Moreover, welcome to the world of access control. Technology continues to evolve the way we do business, the types of devices that we use, the new threat vectors, and how we protect our valued assets. Through all these changes, organizations need intelligent solutions to enforce corporate policy in the access technologies that are deployed.
This book is designed to help you prepare for the Cisco CCNP Security 300-208 SISAS (Implementing Cisco Secure Access Solutions) certification exam, which is one of the four required exams to achieve the Cisco CCNP Security.
Goals and Methods
This book will help the reader understand, design, and deploy Cisco’s Secure Unified Access system. This system will combine 802.1X, profiling, posture assessments, device onboarding, and guest lifecycle management.
The reader will learn all the items that make up the SISAS 300-208 exam blueprint in a realistic method using building blocks of information. Each chapter builds on the knowledge learned in the previous chapters.
How This Book Is Organized
Although you could read this book cover-to-cover, it is designed to be flexible and allow you to easily move between chapters and sections of chapters to cover only the material you need. If you do intend to read them all, the order in which they are presented is an excellent sequence.
Chapters 1–23 cover the following topics:
![]() Chapter 1, “CCNP Security Certification,” discusses the CCNP security certification with an overview and the contents of the SISAS 300-208 exam. It includes a discussion on how to take the SISAS exam and the exam’s format. Additionally, features of the book and exam preparation methods are covered.
Chapter 1, “CCNP Security Certification,” discusses the CCNP security certification with an overview and the contents of the SISAS 300-208 exam. It includes a discussion on how to take the SISAS exam and the exam’s format. Additionally, features of the book and exam preparation methods are covered.
![]() Chapter 2, “Fundamentals of AAA,” builds a strong foundation for the concepts of authentication, authorization, and accounting (AAA). Comparisons and examples of the current AAA technologies and purposes are provided.
Chapter 2, “Fundamentals of AAA,” builds a strong foundation for the concepts of authentication, authorization, and accounting (AAA). Comparisons and examples of the current AAA technologies and purposes are provided.
![]() Chapter 3, “Identity Management,” covers the many identity sources and how they work as related to secure network access.
Chapter 3, “Identity Management,” covers the many identity sources and how they work as related to secure network access.
![]() Chapter 4, “EAP over LAN (also Known as 802.1X),” discusses the IEEE standard for port-based network access control, its history, its progression, and the current state of the art.
Chapter 4, “EAP over LAN (also Known as 802.1X),” discusses the IEEE standard for port-based network access control, its history, its progression, and the current state of the art.
![]() Chapter 5, “Non-802.1X Authentications,” details MAC authentication bypass (MAB) and the various types of web authentications. This chapter strengthens the foundation built in the first four chapters and is reinforced by Chapters 6, 12, and 13.
Chapter 5, “Non-802.1X Authentications,” details MAC authentication bypass (MAB) and the various types of web authentications. This chapter strengthens the foundation built in the first four chapters and is reinforced by Chapters 6, 12, and 13.
![]() Chapter 6, “Introduction to Advanced Concepts,” builds on the strong foundation and starts to expand the reader’s knowledge base with an introduction into technologies such as profiling, posture, and BYOD.
Chapter 6, “Introduction to Advanced Concepts,” builds on the strong foundation and starts to expand the reader’s knowledge base with an introduction into technologies such as profiling, posture, and BYOD.
![]() Chapter 7, “Cisco Identity Services Engine Architecture,” discusses the design of Cisco ISE, personas, and general deployment model.
Chapter 7, “Cisco Identity Services Engine Architecture,” discusses the design of Cisco ISE, personas, and general deployment model.
![]() Chapter 8, “A Guided Tour of the Cisco ISE Graphical User Interface,” walks the reader through the many screens that make up the Cisco ISE graphical user interface.
Chapter 8, “A Guided Tour of the Cisco ISE Graphical User Interface,” walks the reader through the many screens that make up the Cisco ISE graphical user interface.
![]() Chapter 9, “Initial Configuration of Cisco ISE,” guides the reader step-by-step through the bootstrapping and initial setup of Cisco ISE.
Chapter 9, “Initial Configuration of Cisco ISE,” guides the reader step-by-step through the bootstrapping and initial setup of Cisco ISE.
![]() Chapter 10, “Authentication Policies,” discusses the aspects of authentication policies, authentication methods, protocols, conditions, and results. The reader will learn about accessing the identity sources described in Chapter 3 to verify and validate the identity of the user or device attempting network access.
Chapter 10, “Authentication Policies,” discusses the aspects of authentication policies, authentication methods, protocols, conditions, and results. The reader will learn about accessing the identity sources described in Chapter 3 to verify and validate the identity of the user or device attempting network access.
![]() Chapter 11, “Authorization Policies,” discusses the aspects of authorization policies, attribute sources, conditions, and results. The reader will learn about leveraging the identity learned in Chapter 11, accessing attributes of that identity, and utilizing those attributes to form the access control decision.
Chapter 11, “Authorization Policies,” discusses the aspects of authorization policies, attribute sources, conditions, and results. The reader will learn about leveraging the identity learned in Chapter 11, accessing attributes of that identity, and utilizing those attributes to form the access control decision.
![]() Chapter 12, “Implement Wired and Wireless Authentication,” discusses the enabling of 802.1X and non-dot1x authentication and configuring the authorization policy to send the appropriate results.
Chapter 12, “Implement Wired and Wireless Authentication,” discusses the enabling of 802.1X and non-dot1x authentication and configuring the authorization policy to send the appropriate results.
![]() Chapter 13, “Web Authentication,” builds on the knowledge obtained in Chapter 5; this chapter puts the various web authentication mechanisms into play in the network access policies.
Chapter 13, “Web Authentication,” builds on the knowledge obtained in Chapter 5; this chapter puts the various web authentication mechanisms into play in the network access policies.
![]() Chapter 14, “Deploying Guest Services,” discusses extending the authentication and authorization policies with guest lifecycle services, including sponsored and self-registering guests.
Chapter 14, “Deploying Guest Services,” discusses extending the authentication and authorization policies with guest lifecycle services, including sponsored and self-registering guests.
![]() Chapter 15, “Profiling,” discusses the network configuration and ISE configuration related to profiling and profile data collection. Additionally, the chapter focuses on the profiling feed service and profile policies themselves.
Chapter 15, “Profiling,” discusses the network configuration and ISE configuration related to profiling and profile data collection. Additionally, the chapter focuses on the profiling feed service and profile policies themselves.
![]() Chapter 16, “Certificate-Based Authentications,” discusses the use of end-entity certificates for authentication with EAP-Transport Layer Security (EAP-TLS). X.509 certificates, the signing of certificates, as well as the authentication process are examined in detail.
Chapter 16, “Certificate-Based Authentications,” discusses the use of end-entity certificates for authentication with EAP-Transport Layer Security (EAP-TLS). X.509 certificates, the signing of certificates, as well as the authentication process are examined in detail.
![]() Chapter 17, “Bring Your Own Device,” discusses the use of personal devices on the corporate network, differentiating between corporate and personal devices, and the onboarding of devices with Native Supplicant Provisioning (NSP). The ISE policies as well as the network device configuration are examined in detail.
Chapter 17, “Bring Your Own Device,” discusses the use of personal devices on the corporate network, differentiating between corporate and personal devices, and the onboarding of devices with Native Supplicant Provisioning (NSP). The ISE policies as well as the network device configuration are examined in detail.
![]() Chapter 18, “TrustSec and MACSec,” discusses the concepts and use of security group tags (SGTs), as well as the classification, propagation, and enforcement of those SGTs.
Chapter 18, “TrustSec and MACSec,” discusses the concepts and use of security group tags (SGTs), as well as the classification, propagation, and enforcement of those SGTs.
![]() Chapter 19, “Posture Assessment,” discusses endpoint compliance checking, the agents, and provisioning of the agents. The chapter dives into the posture policies themselves and integrating posture to the authorization policy.
Chapter 19, “Posture Assessment,” discusses endpoint compliance checking, the agents, and provisioning of the agents. The chapter dives into the posture policies themselves and integrating posture to the authorization policy.
![]() Chapter 20, “Deploying Safely,” examines a phased deployment approach that enables the administrator to implement ISE in the network environment in a safe and staged method using Monitor-Mode before moving a switch or location into Low-Impact Mode or Closed Mode.
Chapter 20, “Deploying Safely,” examines a phased deployment approach that enables the administrator to implement ISE in the network environment in a safe and staged method using Monitor-Mode before moving a switch or location into Low-Impact Mode or Closed Mode.
![]() Chapter 21, “ISE Scale and High Availability,” describes how to configure ISE nodes in a distributed environment, installing ISE patches, using node groups, promotion of secondary to primary roles, and an introduction to the load-balancing of ISE PSNs.
Chapter 21, “ISE Scale and High Availability,” describes how to configure ISE nodes in a distributed environment, installing ISE patches, using node groups, promotion of secondary to primary roles, and an introduction to the load-balancing of ISE PSNs.
![]() Chapter 22, “Troubleshooting Tools,” extends the validation and troubleshooting lessons learned throughout the book by describing and discussing the many troubleshooting tools within ISE and the network devices themselves.
Chapter 22, “Troubleshooting Tools,” extends the validation and troubleshooting lessons learned throughout the book by describing and discussing the many troubleshooting tools within ISE and the network devices themselves.
![]() Chapter 23, “Final Preparation,” discusses the ways in which to prepare for the exam, from study methods to what to expect on exam day.
Chapter 23, “Final Preparation,” discusses the ways in which to prepare for the exam, from study methods to what to expect on exam day.
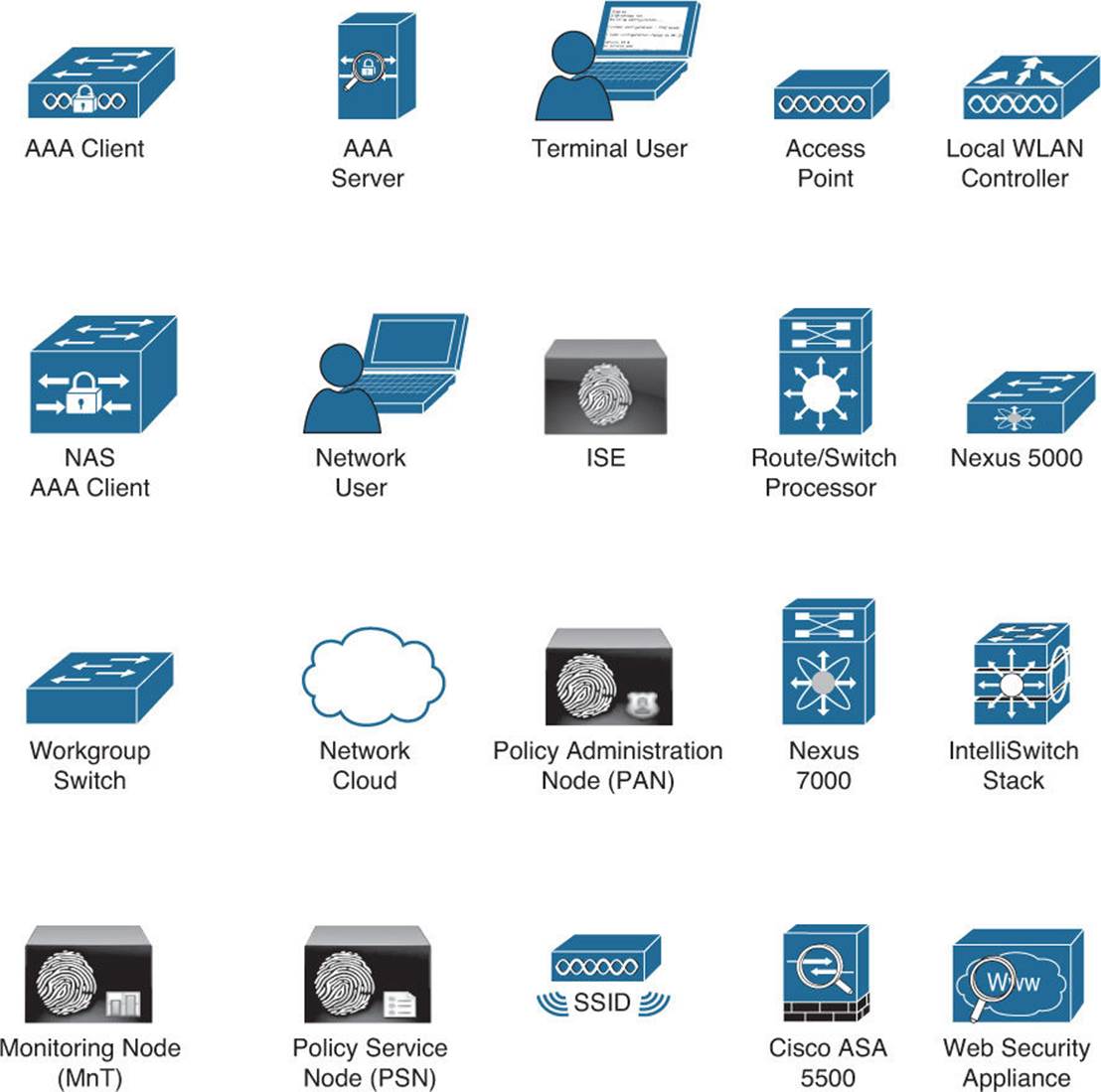
Icons
Command Syntax Conventions
The conventions used to present command syntax in this book are the same conventions used in the IOS Command Reference. The Command Reference describes these conventions as follows:
![]() Boldface indicates commands and keywords that are entered literally, as shown. In actual configuration examples and output (not general command syntax), boldface indicates commands that are manually input by the user (such as a show command).
Boldface indicates commands and keywords that are entered literally, as shown. In actual configuration examples and output (not general command syntax), boldface indicates commands that are manually input by the user (such as a show command).
![]() Italics indicate arguments for which you supply actual values.
Italics indicate arguments for which you supply actual values.
![]() Vertical bars (|) separate alternative, mutually exclusive elements.
Vertical bars (|) separate alternative, mutually exclusive elements.
![]() Square brackets [ ] indicate optional elements.
Square brackets [ ] indicate optional elements.
![]() Braces { } indicate a required choice.
Braces { } indicate a required choice.
![]() Braces within brackets [{ }] indicate a required choice within an optional element.
Braces within brackets [{ }] indicate a required choice within an optional element.